(Presentation and polish isn’t quite so important on this part of the internet.) Click on any website...
When a link is submitted, TOR66 compiles the final results by indexing content on the onion site....
SecureDrop is a really awesome Tor service that can be used to share information without revealing your...
Scannable barcodes and encoded magnetic strips ensure they work in any system, whether it’s a nightclub, store,...
Taking the necessary precautions makes tracing your activities on the dark web difficult. Although the Tor browser...
Clicking a bad link on the dark web can expose you to phishing scams, malware infections, or...
Although the underground internet world is rife with everything bad, it also hosts positive elements. Keybase also...
Russian Market is considered to be one of the most popular, reliable, and valuable marketplaces. Unlike the...
“Hidden Answers” is a community in Darknet, where any user can ask about the use and the...
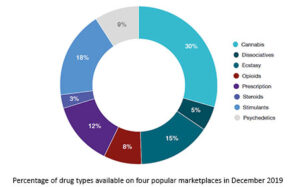
Silk Road not only aggregated thousands of drug vendors, it created a user-friendly interface that resembled a...