Ares implements end-to-end encryption for all communications and transactions. Your data remains secure from prying eyes, with automatic PGP encryption for sensitive information. For example, after the closure of the AlphaBay marketplace, other marketplaces, namely Hansa and Dream Market, experienced an abnormal spike in activity. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address.
Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. This marketplace focuses on selling stolen financial data, such as BINs (Bank Identification Numbers), RDP/VDS access, and verified crypto accounts for money laundering. These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack.
How Darknet Index Helps You Get Valid, Up To Date Links
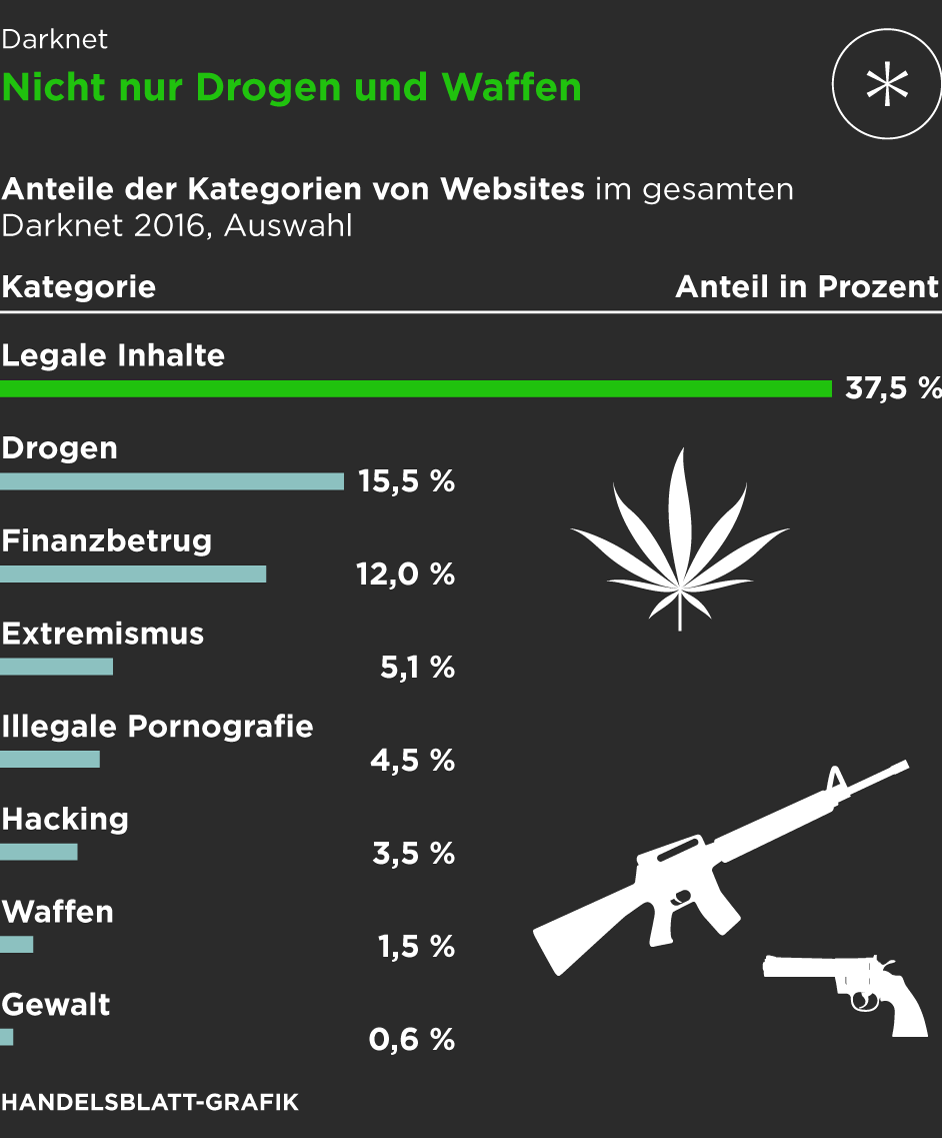
- Dark web marketplaces are mostly hubs for illicit goods and activities, posing serious risks to users and the wider community.
- If the buyer or seller gets caught, there are significant legal ramifications.
- The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted.
- Unlike traditional payment methods cryptocurrencies don’t require personal details like credit card numbers or bank accounts making the transactions more private.
- Simply put, onion sites are websites that are hosted on the Tor darknet that use the “.onion” top-level domain instead of “.com,” or “.gov” for example.
The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection.
Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. Detailed stats on listings, trade volumes, and vendor counts across the top darknet markets.
Shuttered Dark Web Marketplaces
It’s a paid service, and while it’s extremely secure you will need another email address to sign up, which can leave traces of your true identity without you realizing. The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors. The Russian Market has been around since 2019 and is one of the more prominent dark web marketplaces. The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control.
How Darknet Markets Work, Staying Updated, And Getting Valid Links: A Complete Guide

These features collectively make darknet markets a secure and reliable option for the drug trade, meeting the evolving needs of their user base. DarkMatter is a darknet marketplace built for those who demand both power and discretion. With a futuristic design and advanced encryption protocols, DarkMatter provides a seamless, secure trading environment.
After that, many other marketplaces kept trying to take its place and become the top dark web market. However, legal bodies and law enforcement operations made this impossible and shut down these illegal communities. Genesis Market and BidenCash, two top dark web marketplaces, were also shut down in 2023 and 2025, respectively.
Access From Any Onion Mirror
- The sites listed below are well-established and trusted by the general darknet community.
- The first notable marketplace, Silk Road, launched in 2011 by Ross Ulbricht (aka Dread Pirate Roberts), revolutionized online black markets by integrating Tor, Bitcoin, and an escrow system.
- It may take anywhere from 15 seconds to several minutes for a page to load, depending on network and site demand.
- For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow-based exchange that made multiple transactions with Hydra-linked addresses.
- By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited.
- One of the key factors driving the success of darknet markets is the vendor rating system, which allows buyers to evaluate sellers based on product quality, delivery speed, and communication.
The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities. Through the dark web, users in places of high censorship can also access information and news.
These platforms leverage advanced encryption technologies, such as Tor and onion routing, to ensure that transactions remain private and untraceable. The integration of multi-signature escrow systems further minimizes risks, ensuring that funds are released only when both parties are satisfied. The darknet has become a cornerstone for secure and reliable drug trade, offering users a platform that prioritizes privacy and efficiency. In 2025, the best darknet markets have refined their systems to ensure seamless transactions and user safety. These platforms rely on advanced security protocols, such as end-to-end encryption and multi-signature escrow systems, to protect both buyers and vendors. In 2025, the darknet continues to provide a secure platform for the exchange of goods, with drug trade being one of its most prominent sectors.
It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video. Articles cover topics like cold wallet practices and phishing recognition. The official Abacus onion darknet addresses are provided for secure access. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. This ability of dark web communities to thrive in disruptions reflects how dark web market users have become experts at adapting to risks, managing disruptions and rebuilding quickly.
Advanced Tips:
The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers. The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud. TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime.
Alphabay Reaches 60,000 Listings
Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use.
Popular Dark Web Marketplaces

This list has been created mainly to help prevent phishing, impersonation and to direct market users to a safe relevant channels. We can not guarantee the validity of all information posted below, but we will do our best to keep this list up-to-date. As always, do your own research, make your own choices, only you are responsible for your choices and the possible consequences. The sites listed below are well-established and trusted by the general darknet community. All of the sites below have passed certain fundamental requirements to be listed on here. This can be stopped if law enforcement agencies can break any link, particularly dark web marketplaces, in the chain.
Trading Tips
Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device. While this market started in Canada in 2021, WeTheNorth now sells to both Canadian and international users. It’s a market for fake documents, hacking software, and financial fraud services. WeTheNorth has a strong community vibe, with an active forum where users interact and share updates. Unlike regular e-commerce sites, markets on the dark web often deal with illegal or highly restricted goods and services, such as fake documents, hard drugs, and hacking services. Sure, you might come across listings for legit products like handcrafted jewelry or digital art, but those are few and far between.
How Do I Use A VPN With Tor?

That’s exactly what happens when it comes to the dark web marketplaces. TorLinks serves as a backup or secondary directory site to the popular Hidden Wiki. It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers. These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack.



