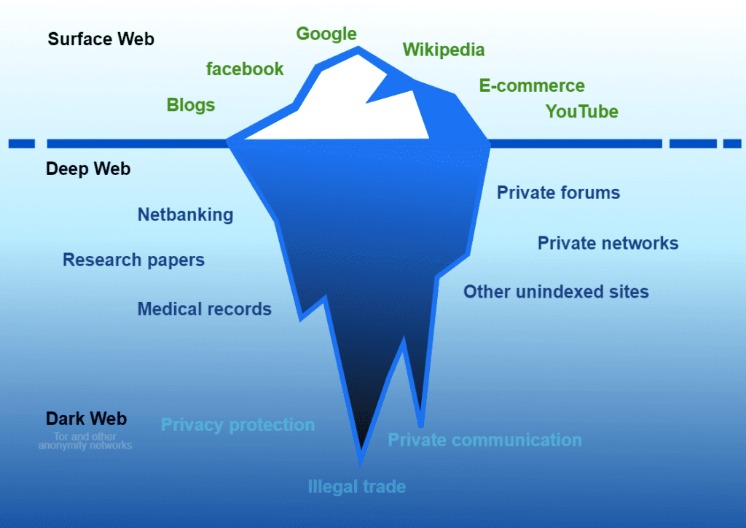
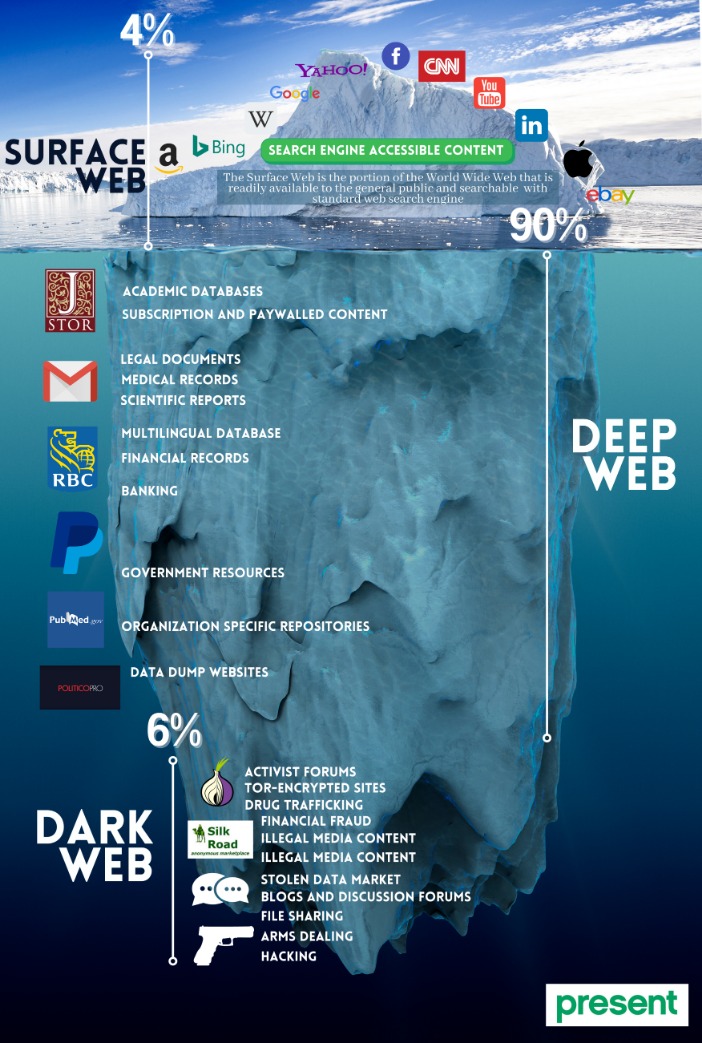
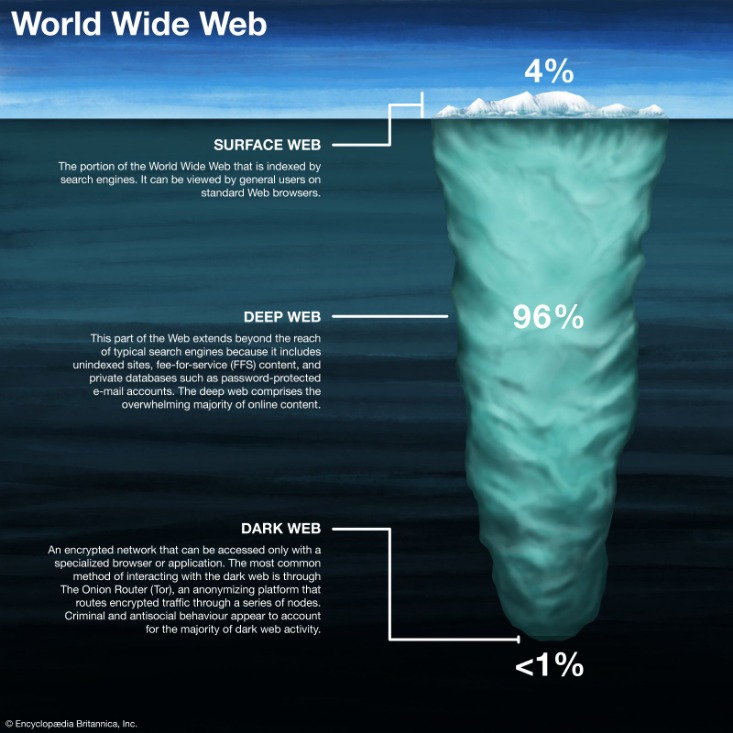
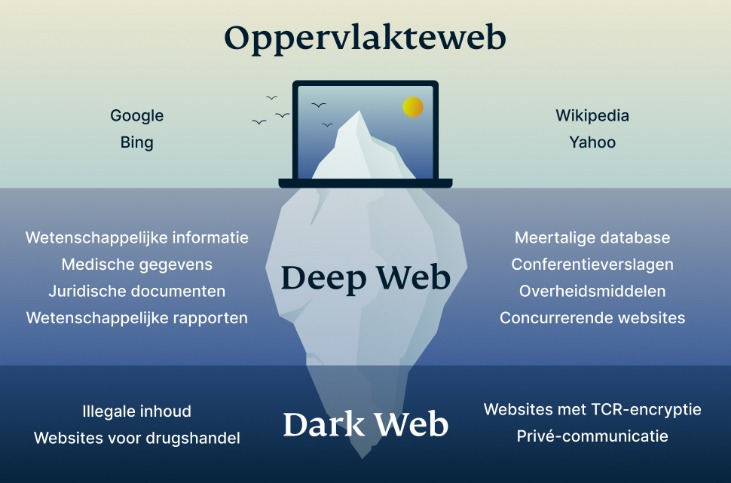
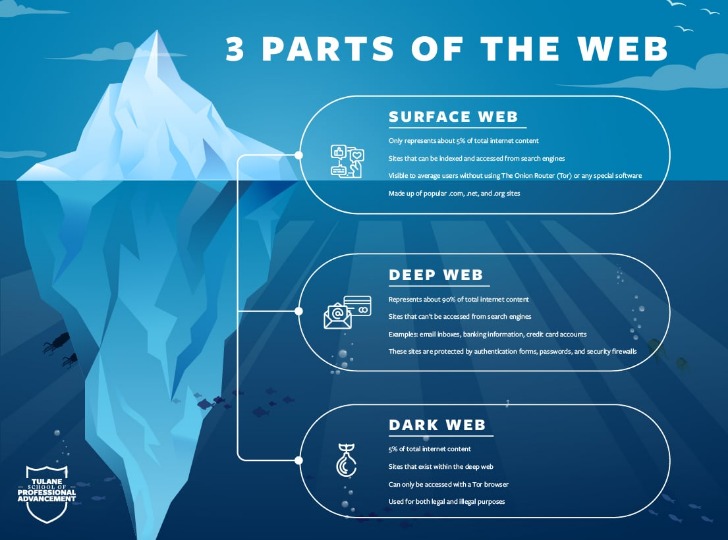
Another term for the internet we all know and use daily is the “regular” internet. Although there are many hypotheses, nobody can be certain about these numbers. Surprisingly, the tiniest portion of the web is typically the most popular and accessible. It’s challenging to quantify exactly how many people use the dark web, as it operates on anonymity.
How To Access The Dark Web On An IPhone
It’s a platform for privacy and free speech, offering resources for individuals in countries with restrictive internet policies. The dark web hosts educational materials, whistleblower sites, and even mainstream media outlets, making it a valuable tool for research and information. Viruses and hacker forums are prevalent, with various types of malware and opportunities for illegal hacking services, which could compromise your personal devices. Webcam hijacking, through remote administration tools, presents a privacy invasion risk, highlighting the importance of physical safeguards like covering webcams when not in use. Furthermore, the dark web’s reputation often attracts curious individuals who are unaware of the potential risks.
Can I Access The Dark Web On My Phone?
Examples of the deep web include any websites that are behind a paywall or require login credentials. Most internet users access the deep web several times a day to perform common tasks, such as checking email, accessing a bank account, or reviewing health or school records. The deep web constitutes over 90% of online content and is inaccessible via search engines. You should avoid illegal activities on the dark web, including drug trafficking, human trafficking, and the sale of stolen information. It’s also essential to avoid sharing personal information or engaging in any activity that could compromise your anonymity or put you at risk of cybercrime.
The group provided bulletproof hosting (BPH) services to the cybercriminals that breached health insurer Medibank Private. “BPH providers are resistant, but not immune, to takedown efforts from law enforcement and requests for cooperation,” AFP says. Most of the content online sits on the Deep Web, which is not accessible via search engines, like the world wide web is. That is because the Deep Web hosts information that is private for a range of reasons, mainly security and privacy related. If you use the right tools, like Norton 360 to protect against malware and phishing, stick to trusted sources, and avoid suspicious sites, your risk is much lower. Think of it like walking through an unfamiliar part of town — it helps to stay alert, research, and know which places to avoid.
Tips For Safe Access To The Dark Web
The threat can extend to your entire network of devices connected to the internet. All in all, it is not illegal to access the dark web, but it can create issues for you. If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks. For example, it maintains your privacy and enables you to access untraceable content and services. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
Know Where You’ll Visit
No, simply accessing the dark web using Tor or other anonymizing browsers is not illegal. However, engaging in illegal activities on the dark web, such as viewing child pornography, selling drugs, or participating in other illicit transactions, is against the law. It is important to differentiate between the tool (Tor) and the actions performed using that tool.
This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see. Despite its legitimate uses, cryptocurrency’s untraceable payment nature has raised concerns around money laundering and illicit trade, driving regulatory scrutiny. DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity.
Has Anyone Ever Been Arrested For Using The Dark Web?
The U.S. Naval Research Laboratory developed the precursor to the Tor (The Onion Router) project during this period as a means to protect government communications. These sites offer access to illegal streaming of pirated movies, TV shows, sports events, or other copyrighted content, often in high quality. These sites bypass copyright protection and may be accessed only on the Dark Web to avoid legal scrutiny. These are platforms where leaked or stolen data, including personal information, passwords, and credit card details, are bought and sold. They often provide access to vast amounts of compromised data from previous hacks or breaches.
Evaluating The Pros And Cons Of The Dark Web
Once a user installs a dark web browser on a device, it functions like a regular browser. That said, it can be difficult for users to find the material they are looking for on the dark web. Addresses tend to be a mix of random numbers and letters, making them challenging to remember or access manually. Addresses also change frequently due to the transient nature of many dark web actors. Finally, because the dark web routes all traffic through a series of proxy servers, which are operated by thousands of volunteers around the world, the search process is typically very slow. The dark web offers both benefits and risks for users going into it, but the intent of the user will also impact this.
What Is Cyber Threat Intelligence?
- Many countries, such as Qatar, China, Cuba, Russia, and Turkey, censor internet content promoting political dissent.
- This feature has given rise to misconceptions, such as the assumption that all dark web activities are criminal, overshadowing its legitimate uses.
- Some dark websites serve as platforms for whistleblowers to anonymously share sensitive information.
- The indie game Sad Satan was claimed to have been found via the dark web, but inconsistencies in the reporting cast doubt on the story.
- Corporations and governing bodies alike currently participate in unauthorized surveillance of online activity.
The dark web is a smaller segment of the deep web and requires specialized software for access. Unlike the deep web, it places a high emphasis on user anonymity and often hosts sensitive or illicit content. To access the dark web, users must install a specialized browser that supports these protocols, such as the Tor Browser or use special operating systems and networks. You’ll also find dark web sites offering downloads of music, software, games, and much more.
Use The Right Tools: Tor And Beyond
All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.
Obviously not all Tor users, but you never know whether someone might be looking into you. It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity. The dark web is a decentralized web, which means that the data is stored on many different servers around the world.



