Companies must implement strong data security measures, employ encryption, and monitor for data breaches to protect customer and employee information. Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement.
Reddit Subreddits For Darknet Markets
It is not impossible, however, as evidenced by the tracking and disruptions of Dark Web networks such as the Silk Road. When navigating the Dark Web, it is vital to think about online safety. Tor gives access to Dark Web connections without disclosing your IP address or location, so enhancing your anonymity and safety. However, it is vital to realize that even with Tor, there are still potential risks involved with browsing the Dark Web. Therefore, it is necessary to exercise caution and use sound judgment when visiting these sites.
More Forums
There is no need to visit darknet marketplaces yourself to know whether your data was leaked. Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. Still, even with these crackdowns and better defenses, dark web markets just keep coming back. As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. The site allows users to find and buy a vast variety of products and services.
In particular, users searched for safe access points, concerned about the integrity of any remaining mirrors or URLs. Many began to transition to alternative platforms, although none have fully replaced the stature Market held. While darknet markets aren’t entirely risk free they generally offer a much safer alternative than buying drugs or other things in person. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities. The significance here lies in the potential damage to individuals and businesses.
The Hidden Wiki & Co
The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. The Dark Web is formed by Darknet(s), small and large overlay networks of which each require different software, authorizations and methods to access.
- If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine.
- Updates often include security patches that protect you against vulnerabilities and potential breaches.
- The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident.
- Europol says the dark web and other peer-to-peer networks are still the “main platform” for sharing child abuse material.
- While accessing Darknet Markets themselves is typically not against the law in most places, engaging with illicit goods within them is generally considered a crime.
Community Forums
In summary, the Tor Browser is your gateway to the darknet, providing a secure and anonymous way to explore and access resources that are otherwise hidden from the standard internet user. Whether for research, social interaction, or simply the allure of the undiscovered, understanding and utilizing the Tor Browser is crucial for anyone looking to venture into this obscure online realm. The Tor Browser is a unique web browser designed specifically to provide users with privacy and anonymity online. By understanding the hazards you may face in the Dark Web and implementing the precautions outlined above, you’ll be better equipped to minimize your exposure to scams, malware, and identity risks. Remember that good judgment, ongoing education, and constant vigilance are your most powerful tools for maintaining a safe and private Dark Web experience.

Using software originally known as The Onion Router (think layers and layers of encryption), Tor secures traffic by routing it through a network of secure relays that anonymize traffic. These relays are run by volunteers around the world who donate their server bandwidth. If the surface web is the tip of the iceberg and the deep web is what’s below the water, then the dark web is what you’ll find deep in the blackest waters below. The darknet refers to the peer-to-peer network itself, whereas the dark web is the content that is served up on these networks. When you log in to internet banking, you’ve navigated to a specific location online, but one that’s not served up in Google results. The same goes for the different pages that pop up in webmail services, like Gmail, or academic databases on a university network.
How To Find Dark Web Websites
That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites.
- Instead of standard URLs, it uses non‑indexed domains like “.onion” and routes every connection through multiple encrypted relays to mask both server and user identities.
- We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention.
- Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer.
- Unlike traditional payment methods cryptocurrencies don’t require personal details like credit card numbers or bank accounts making the transactions more private.
- That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web.
How Much Is Stolen Data Sold For On Darknet Markets?
However, Cody’s book acknowledges that using the Tor network is not without its risks and challenges. It tells readers that using the network may expose them to malicious software and illegal websites. This book is one of many dark web books that tell beginners what the Tor browser is, how to navigate it, and how to use it to explore the dark web.
Top 13 Dark Web Forums Of 2025 To Monitor
Dark net websites are called “Tor hidden services”, and they can be distinguished from normal websites by their URLs. The dark web offers powerful privacy tools, but it also hosts real dangers—from malware and phishing to deanonymization and law-enforcement traps. You need a full-spectrum security mindset that combines technical setup, behavioral discipline and financial hygiene. There are many link lists, wikis and catalogues where you can find addresses to .onion sites.
The Ultimate 2025 Guide To The Tor Browser

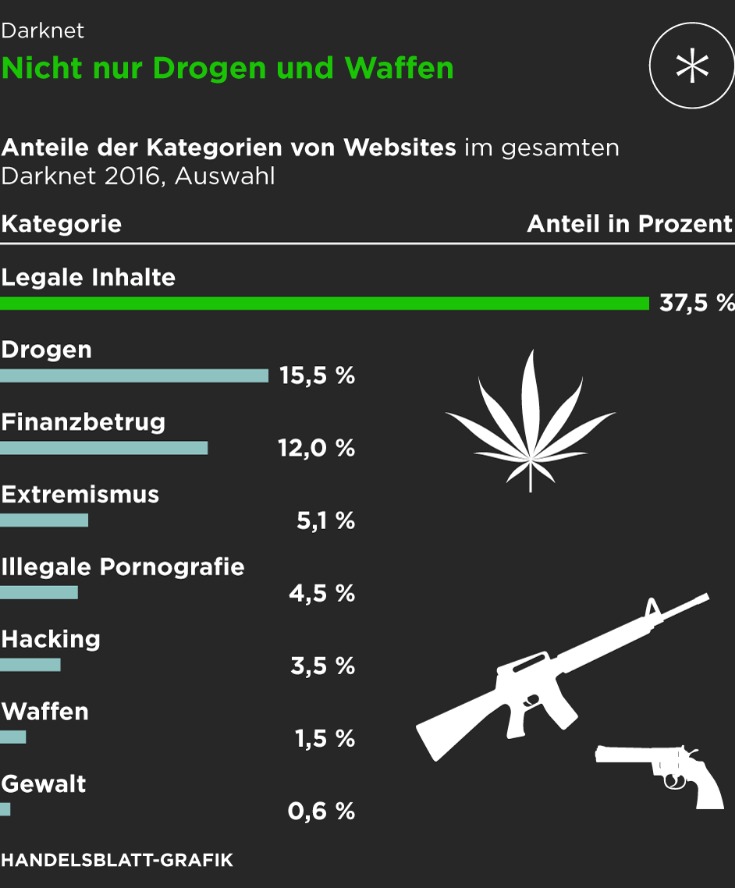
Normal search engines like Google and DuckDuckGo don’t index this part of the web due to its illegal nature. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. Understanding how to access the dark web is valuable for IT leaders, cybersecurity experts, and professionals who need to monitor hidden threats or preserve online privacy. By following this dark web access guide, applying Tor browser safety practices, and knowing when it’s safe to browse the dark web, you can navigate responsibly without compromising your security. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers.
You can also take a look at the blogs & essays section if you want to find some nifty coding resources. At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.