But, honestly, if you are going on the dark just to enjoy free music, we recommend that you go for free torrent platforms on the surface web instead. This is a great resource for users looking to refer to old prices or job listings that have changed or are outdated. This platform is a time capsule with content, primarily web pages. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. The site has a simple interface and offers filters to find books.
BBC Tor Mirror
It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. The early version of Tor was created to mask spy communications. In due course, the framework was remodeled and made public as a secure browser. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged.

Report It To The Authorities (if It’s Safe To Do So)
It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit.
Can WiFi Owners See Your Internet History?
While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.
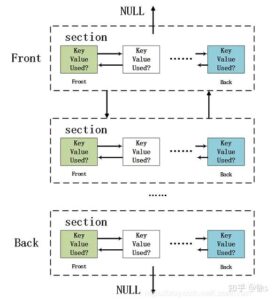
Wie Werden Die Onion-Seiten Gehostet?
In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. ActiveX and Java frameworks are susceptible to being exploited by hackers.
As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.

Email Services
You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services.

Wie Kriegt Man Dark Web Link Listen?
- This ensures greater security and privacy, making it much more difficult for snoopers to get in.
- So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful.
- You only need to upload your PGP key or let the platform create one.
- Unfortunately, it requires you to have an invitation code to create an account.
Avoid entering any real personal details or using existing accounts on dark web sites. Create new anonymous accounts when necessary, using temporary email services. I also recommend covering your webcam and disabling location services before accessing .onion sites.
Alt Address provides disposable email addresses specifically designed for dark web use. This service helps protect your primary email when signing up for .onion services. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours. Since privacy and security are a concern while using the dark web, the websites you visit must have the encryption necessary (HTTPS, preferably) to protect you. However, note that Dark.fail monitors site uptime status and cannot tell whether the site is safe.
Apple Private Relay: Besser Als VPN?
To stay safe and private when visiting any listed sites, ensure you have a VPN and anti-malware installed and enabled. With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity. The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web.
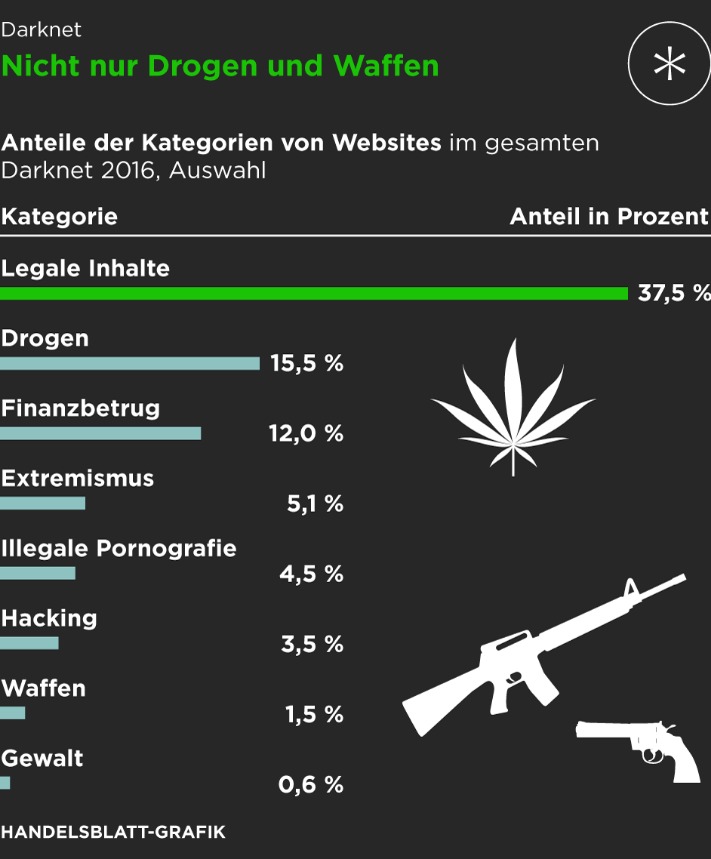
Internet = Gut – Darknet = Böse?
- Its goal is to offer anonymous access to the content without being censored, no matter where you live.
- As we stated earlier, the Hidden Wiki is an unreliable platform.
- Purchases through links on our pages may yield affiliate revenue for us.
- DuckDuckGo is a helpful search engine available on the Tor that allows you to browse the dark and regular web anonymously.
You can access almost any published paper that would have otherwise been hidden behind a paywall. The developers of ProtonMail recommend using the Tor browser to visit the dark web version of the service. This ensures greater security and privacy, making it much more difficult for snoopers to get in.

Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages. This is largely due to harmful elements in the dark web, and Ahmia contains certain questionable and largely illicit links.
In addition, its technology is open-source, and it doesn’t keep your data, which proves it is safe to use. In addition, you can connect your Keybase account with X, GitHub, or Reddit to let people easily trust that they are talking to the actual person. Also, the platform has a feature of automatic deletion of messages – set a timer and they will be deleted after a set period. Keybase is a dark web messaging application that functions much like Signal and WhatsApp, except it is secure and private. This service lets you create your unique domain name with the letters or words you prefer.
If you have a good website, you can launch its Tor version, too. To provide freedom of speech and keep journalism a strong pillar of the economy, the BBC made this Tor mirror. It helps people anonymously use the BBC website without restrictions. The famous social media platform has a prominent presence on the dark web. However, we do not advise readers to log onto this dark web mirror site; doing so would risk their privacy and that of others.