Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise. You may very well end up in the middle of a stakeout that could turn ugly. So, if the website looks fishy, close the tab, and forget about it. Well, there’s a reason why it’s recommended to browse with a minimized or rescaled window – you can be tracked based on your active window’s dimensions (yeah, they really can do that).
- Then, simply click the operating system that you are using and download the file.
- The VPN’s encryption will hide from your ISP the fact that you’re using Tor.
- For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions.
- The Dark Web and Darknets offer valuable spaces if you value privacy, freedom of speech, or research security technologies.If you misuse them, the consequences can be severe.
- Whether you’re exploring it out of curiosity or for legitimate personal reasons, it’s essential to approach this hidden realm with the right knowledge, tools, and security measures.
Consider Using A VPN

Also, it is worth noting that using Tor may draw attention from authorities if they suspect you are engaging in illegal activities or if your online behavior raises suspicion. Generally, it’s important to use Tor responsibly and in accordance with local laws and regulations. However, while using Tor itself is not illegal, some illegal activities can occur through the network, such as the distribution of child pornography or the sale of illegal drugs. It’s important to note that engaging in illegal activities is still illegal, even through the Tor network.
Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
To explain what webpages are on the Deep Web, it will help to first understand a bit about how search engines work. Tell us what you think in the comment section, and keep reading our blog for more informative content. The deep web is where you’ll find private databases, personal email inboxes, bank accounts and academic journals that use paywalls. In a nutshell, anything hidden behind a login screen is part of the deep web. If your Social Security number is found on the dark web, take immediate action to protect yourself. Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service.
I Found The Easiest Way To Delete Myself From The Internet – And It’s Fast
Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows.
Dark Web Search: The Best Dark Web Search Engines In 2025
Accessing the dark web isn’t like surfing the web everywhere else online. While it provides anonymity for privacy advocates and whistleblowers, it’s also a breeding ground for cyber threats. Over half of its listings pose potential risks to individuals and organizations.
If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. In short, even with Tor, there’s no perfect anonymity online, but there are efforts to claw back our power online, says Lewis. To use the dark web safely, use as many privacy-enhancing tools or programs as you can, and do not identify yourself in any way to anyone for any reason. By integrating top-grade security into their operations, organizations can not only reduce their exposure to cyber threats but also reinforce trust in an increasingly data-driven world. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web.
Final Thoughts: Is The Darknet Dangerous?
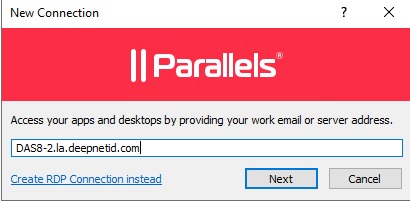
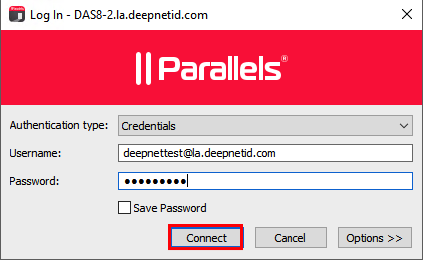
Whited’s rule of thumb is to use the Tor Browser instead of Private Browsing Mode or Incognito Mode. “Contrary to what most people think, these modes do not actually protect your privacy,” she says. Advanced IT services from DeepNet elevate your security, compliance, hosting, disaster recovery, and connectivity. By integrating solutions like advanced SSO, cloud backups, and remote access, your business can boost protection, ensure regulatory compliance, and enhance efficiency.
However, because it’s almost completely anonymous, there are a lot of illegal images, information, products, and services on the dark web. Attempting to even view these can be illegal in many countries and states, so stay well clear of them if you want to keep a clean record and conscience. It all starts with Tor, which keeps your identity under layers of encryption. The Tor browser conceals IP addresses and browsing activity by redirecting web traffic through a series of proxy servers operated by thousands of volunteers across the globe. This process, called onion routing, protects users from surveillance and tracking.
Facebook Onion Site
While DuckDuckGo has made traditional web searching possible on Tor, its results don’t show dark web pages. To access those, you still need to know the URL of the website and enter it in the address bar of the Tor browser. Simply visit the Tor project’s network’s website and download the browser’s version for your operating system. Currently, Tor is available on Windows, Mac, Linux, and Android. There’s also an unofficial version for iOS devices, but it has limited functionalities. With the app downloaded, open and install it by clicking on the.
DuckDuckGo is the best dark web search engine, as it offers an excellent user experience akin to surface web search engines. Its effectiveness in scouring the shadowy depths of the dark web can be likened to what Google does on the surface web. There’s evidence that law enforcement agencies in freer countries operate many exit nodes for monitoring and surveillance purposes.

This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting). There are a few reasons why the dark web isn’t stopped or shut down. First, it’s difficult to track and monitor activity on the dark web since much of it is encrypted. Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites.
Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. Tor was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag. Tor was designed to protect American intelligence communications online.
How To Access The Dark Web (A Step-by-Step Guide)
These tools leave no trace on your device and reduce your exposure even if something goes wrong. Opt for curated sources like Dark.Fail (PGP-verified mirrors) and Ahmia (filters abuse). Treat Hidden Wiki with caution and verify any link via multiple sources.
Another challenge of finding dark web sites is that they don’t often last long. Many sites become defunct quickly, either because they are shut down due to illegal activity, their founders lose interest, or they change addresses and names to avoid detection. Many dark internet users favor Tor which uses a network architecture originally developed by the U.S. Naval Research Lab as a system of decentralized, anonymous nodes to enable anonymous online communication. Standard search engines index these websites and are accessible without special configuration. Being hidden doesn’t translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk.