As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor. The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. Now that you’ve completed the download, it’s time to install the Tor browser on your device.
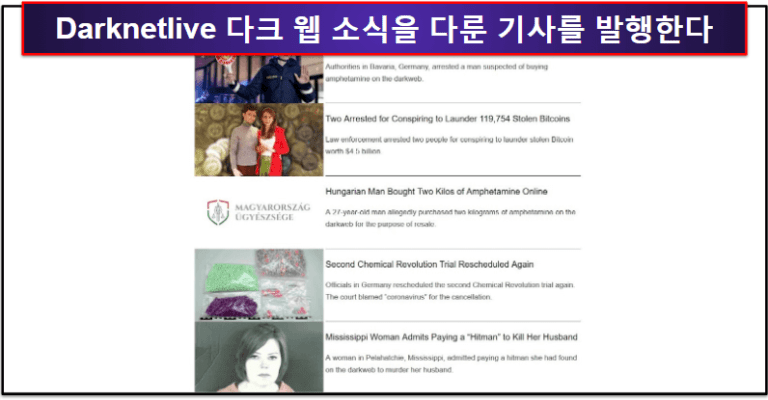
What To Consider When Choosing A Darknet News Source
Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Sections of the dark web are often closed down too, as part of police operations. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges.
Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. City Market is a modern darknet hub designed to emulate the flow and structure of a digital metropolis. With intuitive navigation, categorized listings, and responsive support, City Market offers a smooth experience for users at any level.
Is Darknetlive Compromised?
On top of that, the installation process of Freenet is rather easy. Simply download the file, install the software, and you’re ready to use its web-based interface. I2P can only be used to access hidden sites that are only available on the I2P network.
- The good news is that the BBC Onion site is an international edition.
- On top of that, the provider offers perfect forward secrecy (PFS).
- NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page.
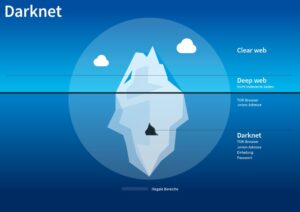
- The deep web is basically all the content that you can’t find using Google or Yahoo search.
- The release of Freenet in 2000 is considered by many as the start or founding of the dark web.
Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019.

Discover the hidden depths of the internet with DarkSearch, the cutting-edge darknet search engine powered by DarkBERT – a pretrained artificial intelligence language model specific to the dark web. TorZon Market, launched in September 2022, supports XMR and BTC payments, features established vendors, and offers a user-friendly platform. Deep Search Engine is a darknet search engine that promotes known scams on the Tor network. Deep Search claims to be built by students who created a new powerful Tor search engine. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.
OnionLive Tor Browser Extension
These sites are all run by the same (admittedly genius) software developer.
Malicious Software
These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links. You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook.
Who Verifies The Safety Of Tor Users? #
Developed to provide a comprehensive solution for darknet users, Black Ops features top vendors, the best fees, unique purchase options, vendor bond… The deep web is made up of content that search engines such as Google do not index. Such data includes medical records, financial information, research papers, private forums and networks, and other content. The site would be reinstated in November,6 with a revamped user interface, and remains active as of September 2022.
What Is Tails Software Used For?
The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime. ProPublica is a popular online publication that won five Pulitzers in 2016. It aims to expose abuses of power and betrayal of public trust through investigative journalism.
It allows you to search for images, maps, files, videos, social media posts, and more. Your queries will be submitted through HTTPS POST to avoid keywords from appearing in the web server logs. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world.
While some studies have claimed that illegal Bitcoin activity is as high as 44%. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites.
Avoid using payment methods that can easily expose your identity. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments.
When both buyers and sellers are anonymous, the credibility of any ratings system is dubious. Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. Law enforcement officials are getting better at finding and prosecuting owners of sites that sell illicit goods and services.
The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. It is imperative to stay alert and trust your gut when on the web. Many services that are allegedly offered on the dark web are scams.