
Some marketplace operators first build trust by running a legitimate platform. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for. Others sell pirated eBooks, academic materials, and entire premium courses ripped straight from paid platforms.
Understanding The Risks
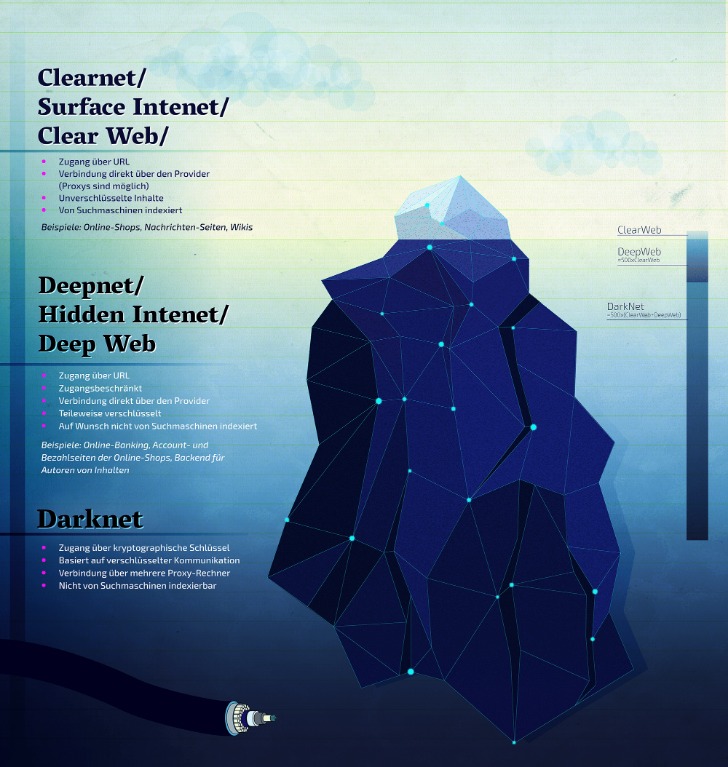
These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. The Darknet is often utilized for secure communication, discreet information or file sharing, anonymous research without identity exposure, and occasionally for engaging in illicit activities. It is also recognized for hosting underground black markets(darknet markets), whistleblowing platforms, and discussion boards that champion freedom of speech. Non-crypto-native money laundering involves off-chain criminal activities, such as narcotics trafficking and fraud. Identifying novel on-chain laundering patterns often mirrors the detection of anomalous fiat-based transactions and patterns.
Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer. The closure led to the arrest of the platform’s founder Ross Ulbricht. According to the United Nations Office on Drugs and Crime (UNODC), all guns are manufactured legally. Therefore, it means that even the guns on the dark web start legally, but along the way from creation to purchasing, a lot of things happen, which makes it easier for the guns to end up on the dark market. The nature of the dark web (anonymity and privacy) opens opportunities for drug dealers to reach a wide customer base across the globe without getting caught. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page.
This material is not intended to provide legal, tax, financial, investment, regulatory or other professional advice, nor is it to be relied upon as a professional opinion. Recipients should consult their own advisors before making these types of decisions. Chainalysis has no responsibility or liability for any decision made or any other acts or omissions in connection with Recipient’s use of this material.

How Do I Verify Onion Routing Links?
The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web. Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. The website has a sleek design and interactive user interface, making it the most preferred choice in terms of user experience.
During his trial, Ulbricht’s defense also pointed to evidence that he advocated for “safer” drug use on Silk Road. The Silk Road black market was a philosophical venture as well as a financial one. The Silk Road definition was a reference to the ancient trans-Eurasian trade route, which brought many different cultures and ideas together in a relatively peaceful manner. The Silk Road website’s founder, Ross Ulbricht (AKA “Dread Pirate Roberts”) sought to emulate this ethos — but failed. Torrez holds your cash tight with escrow, offers a mix from e-books to gear.
- Dark marketplaces Agora, AlphaBay, Dream Market, and Hydra replaced Silk Road and Silk Road 2.0, although all are now defunct.
- Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures.
- When launderers layer funds through many intermediary wallets, the transaction flows are often not simple and linear.
- Cryptocurrencies, while offering enhanced privacy, also present significant risks.
- While there are several darknet markets, each features unique characteristics tailored to various user needs.
Zooming Into Darknet Threats Targeting Japanese Organizations
TRM Labs reports that both its clearnet mirror and hidden-service infrastructure became inaccessible, and the site’s operator, known only as “Vito,” vanished along with users’ escrowed funds. Darkweb-related arrests in Southeast Asia have helped focus attention on how transnational organised crime groups and syndicates operate in the region. Illegal transactions are typically cross-border, emphasising the need for international cooperation, interoperability, and a mutual understanding of the threat. To help detect, investigate, prosecute and prevent this type of cybercrime, capacity building in law enforcement is vital. The regulation of cryptocurrency users and exchanges, especially employing the FATF virtual assets risk-based approach guidelines, will significantly assist in reducing the anonymous transfer of funds.
Incognito Enhances Security
In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year. Other than the Silk Road 2.0, similar marketplaces also emerged, but they all went down sooner or later. The website allows visitors to view all the goods and services on display before they buy something. The quantity, price, and characteristics of the product are all provided. However, the platform lacks an advanced search option and a wallet-free payment option. In April 2016, its APIs were compromised, resulting in stolen messages.
Alphabay Market
Tor Browser, built on Firefox, encrypts your traffic across 3+ relay nodes, enabling access to .onion sites. In 2025, it powers 2.5M+ daily users, with Germany leading in usage (followed by the U.S.). For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Classification Of Sellers And Buyers
The dark web marketplace allegedly amassed up to $168 million in annual revenue. For each entity, we keep track of the cumulative values of the six features for each transaction performed by the entity over time. To be classified as a seller, an entity must simultaneously satisfy the six feature threshold criteria, as follows. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud. Moreover, sensitive personal documents are made available on the dark web. Some things, like medical records, driver’s licenses, and passport information.

Illicit And Risky Use-Cases
Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations. The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes. Platforms known for consistently resolving issues and eliminating fraudulent vendors quickly gain credibility and user loyalty. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem.
It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
Money Laundering And Cryptocurrency

If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private. What’s more concerning is that most of the time, we don’t know about these flaws, and by the time we try to fix them, we come to know it’s too late. Like ransomware, criminals can buy software and inject your devices with viruses.
Cryptocurrency Trading
- Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks.
- Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous.
- Further expanding the aperture, we identified over 1,500 consolidation wallets that have received a total of $2.6B worth of bitcoin in 2024; each of those have received funds from at least ten different wallets.
- Interestingly, while the other categories of sellers show signs of recovery relative to their previous levels, the number of multisellers remains low after that shock (see Supplementary Information Section S4).
- The website has an interface and design similar to other dark web shops.
Third, at any given moment we classify entities as either buyers or sellers. For example, in some cases, a seller in a given market may behave as a buyer in a second market or in the U2U network. This multi-role classification, to be implemented in future work, can help gain a more nuanced understanding of the ecosystem and the structure of the dark web supply chains. To analyse the connectivity of the whole ecosystem, i.e., how markets are connected with each other, we consider sellers and buyers that are simultaneously active on multiple platforms. In particular, multihomers that are sellers in multiple markets are multisellers, and similarly for buyers we have the multibuyers.
Onion sites are websites on the dark web that use the ‘.onion’ top-level domain. They can only be accessed through the Tor browser, which encrypts your connection and masks your IP address, providing anonymity. Some chase banned goods—like a coder I met hunting censored PDFs—others love the mask it offers. The darknet kicked off with Tor back in the early 2000s, cooked up by the U.S.



