
If a Border Force officer suspects an item contains drugs, it’s sent to a special room where inspectors donning protective suits and airflow masks take a closer look. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment. If a seller encourages you to opt for other well-known and commonly used payment methods, then the person is likely to be a scammer, and you must not make any deal with them.
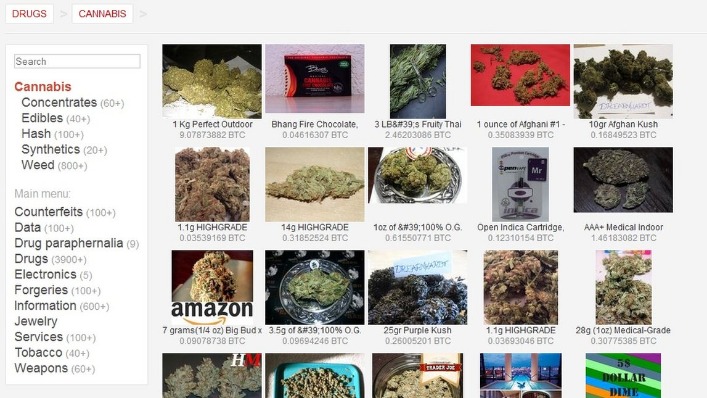
Therefore, you must know how to access dark web marketplaces safely (covered later in this article). Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services. They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions.
- The layers of encryption hide your data and activity from snooping eyes.
- ExpressVPN is an excellent choice for Tor and accessing the Dark Web.
- For instance, you can choose the preferred security levels for enhanced protection.
- They are popular with criminals, because buyers and sellers are largely untraceable.
Dark Web Markets Exposed: Goods, Services, And How They Operate
In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet. This was the initial framework for anonymous communication and file sharing. Later in 2022, the US Naval Research Laboratory built on Freenet’s idea to create a secure and encrypted network for sensitive communications, which was later released to the public as open-source software.
The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored. Detections of small quantity substances are rising, as Aussie drug users continue to flock to online black marketplaces where all kinds of items are easily bought and sent via post. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins.
Q: Is It Possible To Get A Free, First Appointment With My Criminal Lawyer?

The dark web is a hidden segment of the internet, accessible only via special software like Tor, where privacy is paramount and oversight is minimal. While it hosts legitimate forums and whistleblower sites, it’s also a marketplace for cybercrime—and its reach is growing. By mid-2025, several high-profile marketplaces were either hacked, exit scammed, or seized.
The Marketplace As An Arsenal
Although dark web take-downs by cross-border law enforcement operations have had some impact on the availability of those drugs, an ANU report has compared it to a game of whack-a-mole. Other letters detected that morning contained cannabinoid products, produced and sold legally in countries such as Canada and in certain US states such as Washington and Colorado, but imported illegally. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details.
Subscribe To ANU Reporter
This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024). As mentioned earlier, launching a cyberattack doesn’t require any hacking skills.
Hong Kong Dark Report: February 2025
In the end, he was sentenced to life in prison for running one of the largest and most scandalous dark web cases in history. But somewhere between production and purchasing, things can get dirty. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. BidenCash was launched in 2022, and since it became a hot spot for cybercriminals to sell and buy illegal things, including stolen card information and personal data. However, in June 2025, BidenCash’s relevant domains (around 145) were seized by the US Department of Justice.
Use Cryptocurrency For Transactions
The use of the dark web raises suspicion as it shows there is something you want to do privately. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
“Many markets, particularly markets that want to stay operational, will often ban vendors from selling those sorts of products, just like they do with child exploitation materials.” “We found markets close down and pop up again with a refreshed set of security features, price hikes or even self-regulation of the kinds of products sold to avoid the spotlight. Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. Border Protection and police service resources are already stretched slim.
This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address.

As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive. They even have a Telegram channel to provide their clients with live updates. Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace.
Separate Your Real Life From Your Online Persona
As a Leading Cybersecurity Company in Australia, we are offering a free 60-minute cybersecurity consultation to help evaluate potential vulnerabilities in your digital environment. Buyers can purchase Ransomware-as-a-Service (RaaS), phishing kits, and malware to launch cyberattacks. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums.



