BleepingComputer has discussed the authenticity with analysts at D3Lab, who confirmed that the data is real with several Italian banks, so the leaked entries correspond to real cards and cardholders. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data. Many cyberfraudsters view themselves as cyber vigilantes and are personally more willing to scam the government out of funds instead of their neighbor next door. In December, USA Today reported there had been an estimated $36 Billion USD stolen across U.S. unemployment benefits. I’ve worked with family-owned businesses that nearly went under after getting hit with a wave of fraudulent purchases. The pricing varies based on the card type, with premium cards from certain banks fetching higher prices.
Transaction Fraud How To Protect Your Business & Customers

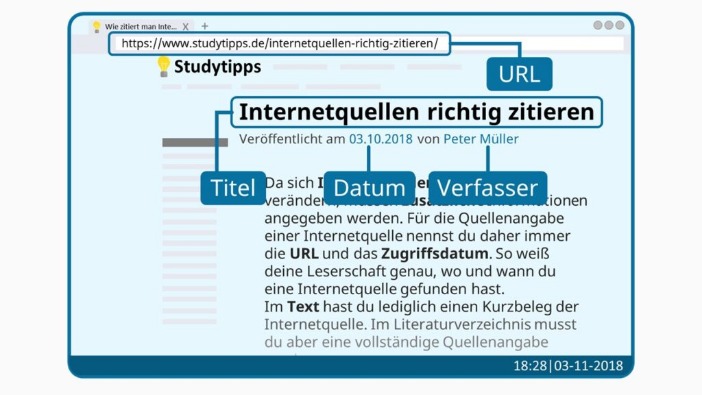
Stolen card details often end up on the dark web marketplace for a quick profit, and this can happen before you even know about it. Vendors sell additional information about the cardholder, known as “fullz”, which includes the cardholder’s social security number, street address, birth date, and more. While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams.
Picus Blue Report 2025 Is Here: 2X Increase In Password Cracking

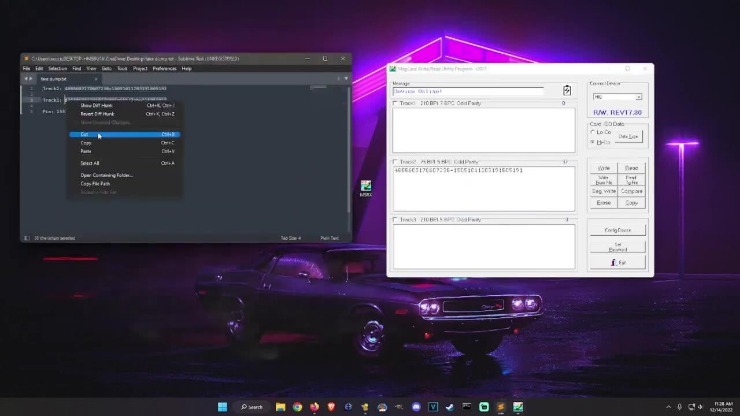
When a hacker writes up new malware, steals a database, or phishes someone for their credit card number, the next step is often toward dark net marketplaces. These black markets allow buyers and sellers to make anonymous transactions using a combination of encrypted messages, aliases, and cryptocurrency. It is worth noting that engaging with illegal transactions on the deep web always carries risks and legal consequences. While Savastan0 may dominate this space with their superior products and services, potential buyers must exercise caution before making any purchases or engaging in illegal activities involving CC Dumps Bins.
How To Protect Your Identity While Browsing The Dark Web

With unparalleled quality assurance protocols in place, they ensure each dump contains accurate information needed for fraudulent purposes. Welcome to the mysterious and shadowy realm of the Deep Web, where anonymity reigns supreme and hidden treasures await those daring enough to venture into its depths. Today, we shine a light on one enigmatic figure that has made waves in this underground world – Savastan0 CC Sales CC Dumps Bins. Brace yourself for an exhilarating journey as we unveil the secrets behind their dominance in this clandestine market. Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web. It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures.
CISOs Brace For Supply Chain Attacks With Proactive Attack Surface Monitoring
“The most important thing is for people to keep an eye on their transactions and report any fraud immediately,” Krebs says. One of the largest known underground shops, Joker’s Stash, generated more than $1 billion before getting shut down in February, according to Gemini Advisory. A 2019 data leak of another shop, BriansClub — which appears to have been by a competitor, according to Threatpost —shows how pervasive this trend has become. As data breaches become more common, and scammers grow more sophisticated, this is a reality many people are having to contend with. This integrated approach, combining insights from FraudAction and the protection of Outseer 3-D Secure, enhances fraud prevention, positioning the institution as a guardian of customer trust in the dynamic fraud landscape. The closures are unlikely to spell the end of darknet markets as new ones will no doubt emerge.
Credit Cards Skimmed And Used As Marketing Tool
It is crucial to take necessary precautions such as using secure connections, utilizing anonymous browsing tools like VPNs or Tor networks, and ensuring personal information remains protected at all times. As we delve into the mysterious world of the deep web, it becomes clear that Savastan0 holds a dominant position in the market for high-quality CC Dumps Bins. Their expertise and dedication to providing top-notch products have solidified their reputation among underground communities. In conclusion (without using those words), as we look towards the future of the deep web and Savastan0’s role within it, one thing remains certain – their dominance shows no signs of waning anytime soon. Whether you choose to partake or merely observe from a distance, it is essential to stay informed about emerging trends in cybersecurity while remaining vigilant against potential threats lurking beneath the surface.
- Physical cards are usually cloned from details stolen online, but can be used to withdraw from ATMs.
- Carders target sites without these protections, and some vendors even sell lists of “cardable” sites for a few dollars.
- Customers who lose their card data to fraud may turn to a different card while waiting for a replacement card, threatening the top-card effect of passing all spending across one preferred card.
- This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself.
- And it’s here where Savastan0 CC Sales CC Dumps Bins enters into play—an underground marketplace specializing in selling high-quality credit card dumps obtained from various sources worldwide.
Card Data And Markets
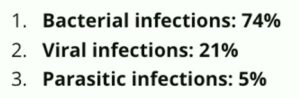
Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. In 2024, the platform grew significantly in popularity, partly because of its strategic acquisition of users from a number of recently shut-down marketplaces, such as AlphaBay and Incognito Market, which had recently closed their doors. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. Sometimes hackers will commit “card-present fraud” by breaching the point of the sale at a physical store. Or they’ll commit “card-not-present fraud,” by hacking a website and stealing the online card information that gets entered into the checkout page. In addition to the risk for payment card holders, the leaked set could also be used in scams or other attacks targeting bank employees.
Carding – Unauthorized Purchases By Fraudsters
Here are some of the now-defunct dark web markets that were notorious for cybercrime. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info.
DarkOwl assesses fraud against government docs, benefits, and employment will increase since the pandemic. Swiping may also refer to the process of using stolen debit card information to collect cash out of an ATM. Variations of this process have been popularized across deep web enthusiasts in the hip hop culture spurring a completely new genre of “scam rap” where the technique is woven into the lyrics of rap songs. DarkOwl has observed this with young scam-rappers such as Teejayx6, as shown in the video below.
Customers
Due to the vast number of scams and scam-attempts that most of us encounter on a daily basis, today’s society has largely become desensitized to fraud as we understand it on the internet. However, very few understand how this criminal economy thrives extensively across the darknet where it takes on a variety of different formats that target individuals and corporations alike. Breachsense monitors the dark web, Telegram channels, hacker forums, and paste sites for external threats to your organization.
These platforms serve as hubs for cybercriminals to buy and sell compromised payment card details. Operating as shadowy corners of the internet, dark web credit card marketplaces facilitate the buying and selling of stolen payment cards. These platforms provide a marketplace for payment card data stolen by a variety of actors, leading to further specialization in crime. While criminals in the past might have stolen card data for their own reuse in carding, modern criminals split into those who capture and skim card data, and carders who take stolen card data and use it to make illicit purchases. Back in the day, carding forums were the busiest of online crime hangouts, selling packs of stolen credit card data to anyone with the cash.
One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. The “special event” offer was first spotted Friday by Italian security researchers at D3Lab, who monitors carding sites on the dark web. If so, this guide will help you automate supply chain risk reports using AI Chat GPT and our News API.