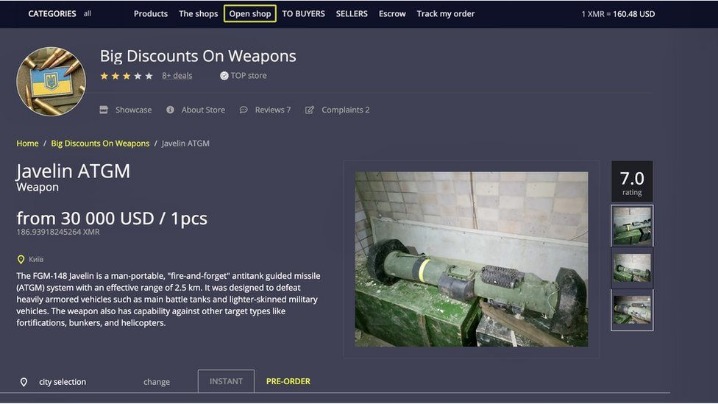
Some of these are well-known, established threats that circulate in this nook of the web. However, others may be taking advantage of the dark web’s reputation to trick users out of large sums of money. Also, some users on the dark web may attempt phishing scams to steal your identity or personal information for extortion.
The Layers Of The Web
By shedding light on the shadowy corners of the cyber threat landscape, it empowers organizations to stay one step ahead of cybercriminals. In the unfortunate event of a data breach, the dark web is usually the first place stolen data appears for sale. Monitoring the dark web allows organizations to quickly identify their stolen data, helping them gauge the extent of a breach and respond effectively. Data often appears on dark web forums such as Breachforums, which threat actors give away for free or sell. What we see and use daily – news websites, online shopping – is commonly referred to as the clear web.
Drugs And Stolen Goods
Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers.
Identity And Data Theft
Beyond the sale of stolen data, the dark web facilitates the proliferation of cyber threats. Tools for hacking, malware, and ransomware are readily available for purchase, lowering the barrier for cybercriminals to launch sophisticated attacks. Forums on the dark web also provide spaces for malicious actors to exchange knowledge, collaborate, and refine their techniques. While the deep web includes legitimate, unindexed content such as private databases and subscription-only platforms, the dark web specifically facilitates anonymity. This feature has given rise to misconceptions, such as the assumption that all dark web activities are criminal, overshadowing its legitimate uses. Beyond its association with cybercrime, the dark web has also become a refuge for whistleblowers, journalists, and individuals in oppressive regimes seeking privacy or secure communication channels.
The Rise And Fall Of Ransomware: Insights From Avast’s Q1/2023 Threat Report
With ZeroBin, you can easily exchange encrypted messages within the dark web. With 256-bit AES encryption, this platform enforces its two-fold service of secure messaging and zero logs of your activity. SecureDrop is a secure hub for journalists and whistleblowers to interact and trade vital information.
The Tor Times

The origins of the dark web, cyber crime and internet censorship across the world. The final relay decrypts the innermost layer and sends the original data to its destination without revealing or knowing the source IP address. It encrypts the application layer of a communication protocol stack and got its name due to its nested nature akin to the layers of an onion.
What To Do If Your Social Security Number Is On The Dark Web
Obscurity is simple to implement but does not secure assets, they’re accessible with the right URL, a massive cyber security risk that often results in data leaks. You can reduce these risks by taking basic precautions—avoiding sharing personal information, steering clear of suspicious sites, and using strong passwords. In addition to conducting disruption operations, governments and international institutions are attempting to directly regulate the cryptocurrencies that are fueling dark web marketplaces. In June 2019, for example, the Financial Action Task Force issued guidance that urges companies processing cryptocurrency transfers to identify both the sender and receiver of fund transfers. The impending launch of Libra, Facebook’s cryptocurrency, will only make this a more pressing concern as the barriers to adopting virtual assets are lowered for Facebook’s nearly 2 billion-plus users. Now map them back to the attack surface graph for added context and to prioritize remediation efforts.
Pro Publica
The service retains no copies of any data that passes through a ProtonMail account. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail. SecureDrop uses Tor to provide a safe way for whistleblowers to contact various news outlets.
Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day. Torch is funded primarily through advertising—purchased in BTC, of course—which is why you’ll find the front page blanketed with old-school banner ads of dubious origins. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. When the dark web is mentioned online, it is usually in tandem with criminal marketplaces and arrests made by law enforcement agencies. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers.

Access The Dark Web Safely
Accessing it through an onion link is much more convenient if you’re unable to directly view it on your screen. Clearly, if you want to form your exclusive private club of family members, friends, fellow journalists, or other close-knit groups, Keybase is a wonderful online platform. It also works with Windows, Android, iOS, macOS, and Linux, ensuring your co-participants can use any device. Switzerland-based Proton (formerly ProtonMail) is one of the most secure email services, and has a reputation for not logging IP addresses. If you care about your privacy on the Internet, no other site comes close.
- Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites.
- Open up Tor, and you won’t suddenly see the dark web staring back at you.
- “The Tor network is another network which sits on top of the TCP/IP internet, stitching the participating computers together into a wholly new network ‘space’, not IPv4, not IPv6, but ‘Onion Space’.”
- Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites.
- Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions.
The Hidden Wiki is a comprehensive starting point for exploring verified dark web links. Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. During my testing, I found its categorized index particularly helpful for discovering trustworthy sites across various topics. Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet. Access to “.onion” domains and anonymous surfing made possible by specialised software like the Tor Browser allows entry only.
In freer societies, it can be a critical whistle-blowing and communication tool that shields people from retribution or judgment in the workplace or community. Alternatively, it can simply deliver privacy and anonymity for those wary of how corporations and governments are tracking, using, and potentially monetizing their data. Today, many organizations maintain a hidden website on Tor, including nearly every major newspaper, Facebook, and even the US Central Intelligence Agency (CIA). This is because a Tor website demonstrates a (sometimes symbolic) commitment to privacy. The New York Times and the CIA, for example, are both hoping to facilitate communication with virtual walk-ins who can provide sensitive information.



