In due course, the framework was remodeled and made public as a secure browser. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
Market Types
However, note that Dark.fail monitors site uptime status and cannot tell whether the site is safe. To stay safe and private when visiting any listed sites, ensure you have a VPN and anti-malware installed and enabled. With ZeroBin, you can easily exchange encrypted messages within the dark web. With 256-bit AES encryption, this platform enforces its two-fold service of secure messaging and zero logs of your activity. In addition, Haystak offers a premium plan that allows deeper search, email alerts, and access to historical content.
Verified Social Channels And News Sites
You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction.
Tips To Stay Safe When Using The Dark Web
If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. On top of that, the provider offers perfect forward secrecy (PFS). A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. Most likely, the native account on your device has full admin permissions by default. Many malware take advantage of this vulnerability to launch an attack.
It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications. Sci-Hub is a massive database that eliminates the barriers to getting scientific knowledge. It contains millions of scientific research documents from around the world.
Such content fuels a dangerous cycle of abuse, violence, and exploitation. The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one. Want to get illegal drugs, fake passports, Trojan, or other cyber attack software?
Cypher Marketplace
The site seeks to liberate information by making it free to individuals and institutions. The website is available on the surface web and has a .onion site. This means you can visit the site anonymously using the Onion browser, especially if you live under an oppressive regime.
Telegram is a widely-used platform for dark web criminals and is a go-to cyberspace for vendors and buyers who use it on a daily basis. This platform is commonly used because of its accessibility, free use, and anonymity. If we add to that the fact that chats are an easy and instant platform for communications, it is no wonder that there are thousands of Telegram groups and channels that are primarily focused on the sale of drugs. Dark web marketplaces, both on the open web and on Tor, operate as decentralized marketplaces, which are by far the most common place for the illegal drug trade, alongside other illegal products.
“Sometimes not when they’re doing the crime, but when they’re just online doing their own personal thing, sometimes they mix up accounts,” Henderson explained. Download Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online. Install Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online. ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books. It often hosts copyrighted materials without permission, violating many countries’ copyright laws. Downloading or distributing such material is against the law and can have legal consequences.
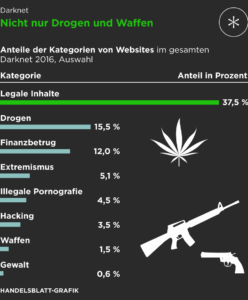
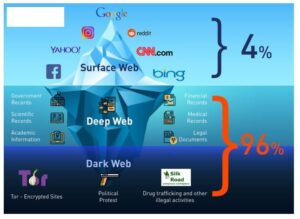
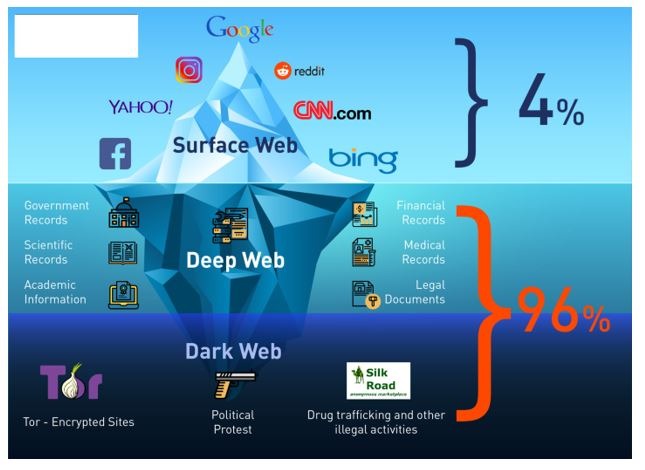
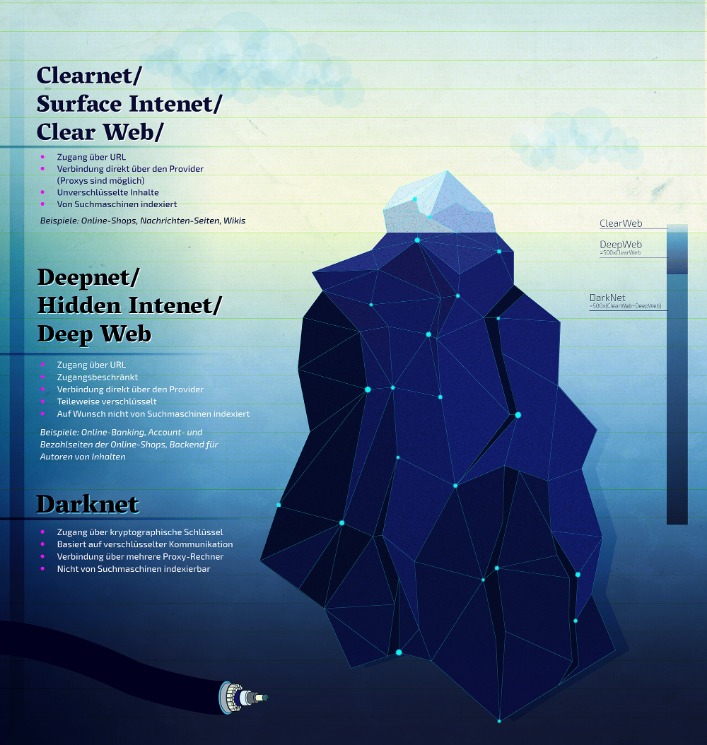
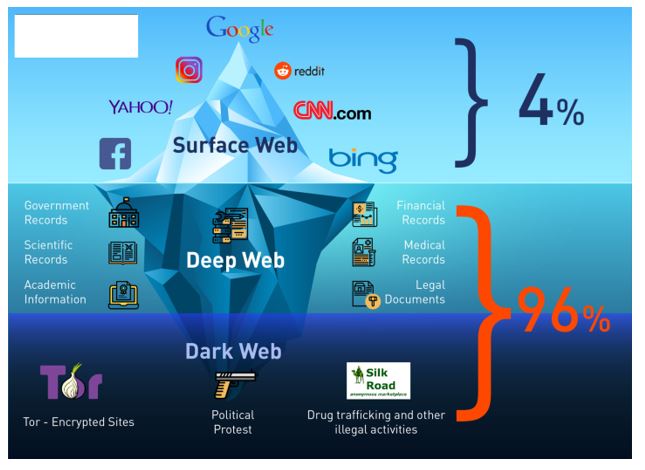
Difference Between Dark Web And Deep Web
- As a result of the action, the platform’s infrastructure in the Netherlands was taken offline and its administrator – a 30-year-old German national – was arrested in Barcelona, Spain.
- Peruvian Cocaine, Fish Scale, Uncut Flake, Synthetic, Columbia and many other types of Cocaine is sold.
- Therefore, the legality of the dark web will mainly depend on how you use it.
- The platform utilizes end-to-end encryption, ensuring it does not store any activity records.
- “But that doesn’t seem to have dented the ecosystem in a major way.”
In fact, everything is in English, and the site picks up users everywhere in the world. People visit this market to buy stolen credit cards, personal data, remote desktop account credentials, and logs gathered from information-stealing malware. Unlike regular e-commerce sites, markets on the dark web often deal with illegal or highly restricted goods and services, such as fake documents, hard drugs, and hacking services. Sure, you might come across listings for legit products like handcrafted jewelry or digital art, but those are few and far between. Usually, it takes a few weeks for buyers to transfer to alternative or new sites. When cops shut that site, they knew users would migrate to any service they could – and many fed to Hansa market, which the cops had seized and allowed to continue operating so they could capture user data.
Top 12 Onion Websites: A Look At The Dark Web
This is no different from the “.net” or “.com” of the regular Internet. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing. As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. The Internet is a vast and complex landscape, much larger than the familiar interface we use every day.
The integration of cryptocurrencies like Bitcoin and Monero further strengthens the anonymity of buyers and sellers, making it nearly impossible to trace financial activities. In our study, a total of 248,359 listings from 10 anonymous online marketplaces and 1,138,961 traces (ie, threads of posts) from 6 underground forums were collected. Among them, we identified 28,106 opioid product listings and 13,508 opioid-related promotional and review forum traces from 5147 unique opioid suppliers’ IDs and 2778 unique opioid buyers’ IDs. A total of 248,359 listings from 10 anonymous online marketplaces and 1,138,961 traces (ie, threads of posts) from 6 underground forums were collected. JCODE and Europol’s European Cybercrime Centre (EC3) continue to compile intelligence packages to identify entities of interest. Parsarad was also indicted by a federal grand jury in the Northern District of Ohio on drug trafficking charges related to the illegal business he ran on the dark web.
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.

Impact Of Law Enforcement And Policy Changes
And if unwanted fentanyl does crop up online, buyers can easily warn each other by way of the review system or the forums. Even if you still have a regular in-person dealer that you trust, they may not know what they’re selling, or, for that matter, be able to find a supplier whose gear isn’t compromised. However, you can trace its roots to the development of technologies like the Tor network or Freenet.
Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr… Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… We also made sure to select only sites that have been around for a considerable amount of time without being taken down or being the subject of any privacy or security scandals.