
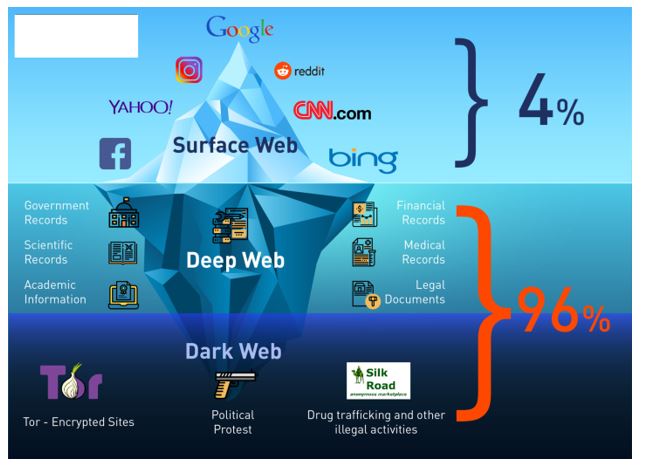
You can access onion sites only through the Tor browser or special network configurations. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity. In the image above, (a) is the surface web, which includes publicly visible websites like blogs, shopping sites, and news sites. (b) is the deep web, which consists of sites that require a login to access like email accounts, banking portals, and subscription services.
- Tor2door’s a standout since 2020 with 20,000+ listings and a custom design that’s not off-the-shelf junk.
- “This is the single most significant law enforcement disruption of the darknet to date,” U.S.
- The use of digital signatures can also help verify the authenticity of users and transactions.
- However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it.
StartPage – User-Friendly Dark Web Search Engine Like Google

BidenCash was launched in 2022, and since it became a hot spot for cybercriminals to sell and buy illegal things, including stolen card information and personal data. However, in June 2025, BidenCash’s relevant domains (around 145) were seized by the US Department of Justice. The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one.
Never Share Personal Information
Some users also share links on encrypted apps like Telegram or Keybase that you can check. Blockchain even has an HTTPS security certificate for even better protection. Dark web markets work in a way that is not like your everyday online shopping.
Specialized Data Repositories
However, the quality of the resources you choose to engage with can make all the difference in ensuring a safer, more productive experience. By applying well-defined criteria, you can more confidently separate valuable platforms from malicious or untrustworthy ones. This article aims to shed light on the more constructive side of the dark web, guiding readers toward reputable resources and reliable information. We’ll cover the foundational principles of anonymity on networks like Tor, discuss how to navigate this hidden realm safely, and emphasize the importance of verifying sources. Throughout, we’ll stress the ethical and legal considerations that come with exploring these lesser-known platforms.
The darknet has become a cornerstone for secure and efficient drug trade, offering users unparalleled privacy and reliability. By 2025, several platforms have emerged as leaders in this space, leveraging advanced encryption, decentralized systems, and user-friendly interfaces to ensure seamless transactions. These advancements will further solidify their position as a secure and reliable option for users worldwide. Pharmaceuticals and recreational drugs remain the most sought-after products on these platforms, with vendors offering a wide range of high-quality substances. The use of encrypted messaging and secure payment methods ensures that transactions remain private and secure, fostering a thriving environment for trade.
The platform is protected from government interference and malicious attacks to protect the user. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted. Although the social application is known for collecting data on its platform, it does not like sharing the information with others. It will offer you an additional layer of encryption to access the deep parts of the internet.
Absence Of Malicious Content And Practices

Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Main News
This is high-level protection; no one can intercept your data or activities. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity.
What Websites Are On The Dark Web?
It contains a good selection of product listings that range over 35,000 items. The website has an interface and design similar to other dark web shops. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services.

Torch — A Long-Standing Dark Web Search Engine With A Wide Index Of Onion Sites
It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance. Mega Market is a new yet popular shop on the dark web that reached a skyrocketing reputation after the closure of the Hydra market. It allows you to buy and sell a wide range of products and services with a good user experience. This site supports PGP encryption and two-factor authentication features.
Dark0de Reborn Market
However, we do not advise readers to log onto this dark web mirror site; doing so would risk their privacy and that of others. We check all comments within 48 hours to ensure they’re real and not offensive. Some sites might use these details for advertising, analytics, or tracking your online preferences.
Haystack is an easy-to-use search engine for .onion sites that weeds out malicious and harmful links. However, with thousands of search results, the danger of clicking the wrong link remains. It’s purely used to search dark sites, and can only be accessed via the Tor browser, and isn’t available on the clear net. Like any other browser, you can search for a relevant keyword using its search bar, and it will show you results if its database has any relevant websites stored. Ahmia has a very strict policy against abusive content, and any link with such content, if reported, is added to a blocklist and isn’t shown in future search results.
Primary Risks And Dangers Of Using Dark-Web Marketplaces
If a seller encourages you to opt for other well-known and commonly used payment methods, then the person is likely to be a scammer, and you must not make any deal with them. Always use a fake name and a temporary email address when you buy something from the dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web.



