While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity. Telegram channels, encrypted messaging apps, and invite-only forums support additional layers of communication and product distribution.
The New York Times
From there, these products are then passed on to distributors, which are the dark web marketplaces in this context. On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. BidenCash was launched in 2022, and since it became a hot spot for cybercriminals to sell and buy illegal things, including stolen card information and personal data. However, in June 2025, BidenCash’s relevant domains (around 145) were seized by the US Department of Justice. Just as there are new entrants, the dark web has its veteran markets too, and Brian’s Club is one such market. It has been in operation for more than a decade since its debut in 2014.
The Emergence Of Marketplaces On The Darknet
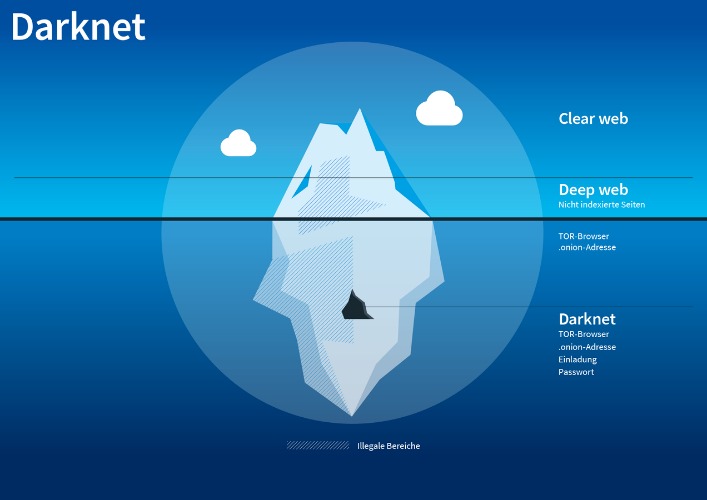
You don’t even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. Alternatively, there’s IPVanish who claim to be the world’s number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here. Another vital precaution is to ensure that your .onion URLs are correct. Onion URLs generally contain a string of seemingly random letters and numbers.
- An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions.
- Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
- Darknet marketplaces may look like regular online stores, but using or even browsing them comes with serious risks.
- Cybercriminals go on dark web marketplaces to buy and sell illicit goods and services.
- The Darknet is often utilized for secure communication, discreet information or file sharing, anonymous research without identity exposure, and occasionally for engaging in illicit activities.
Exploitation Of Anonymity For Harm
Some marketplaces have even mandated Monero-only transactions, underscoring a strong preference for privacy-focused coins over traceable ones. Cryptocurrencies have replaced fiat currencies as the default medium of exchange on the dark web. Bitcoin continues to lead as the most widely accepted digital currency due to its high liquidity and global acceptance.
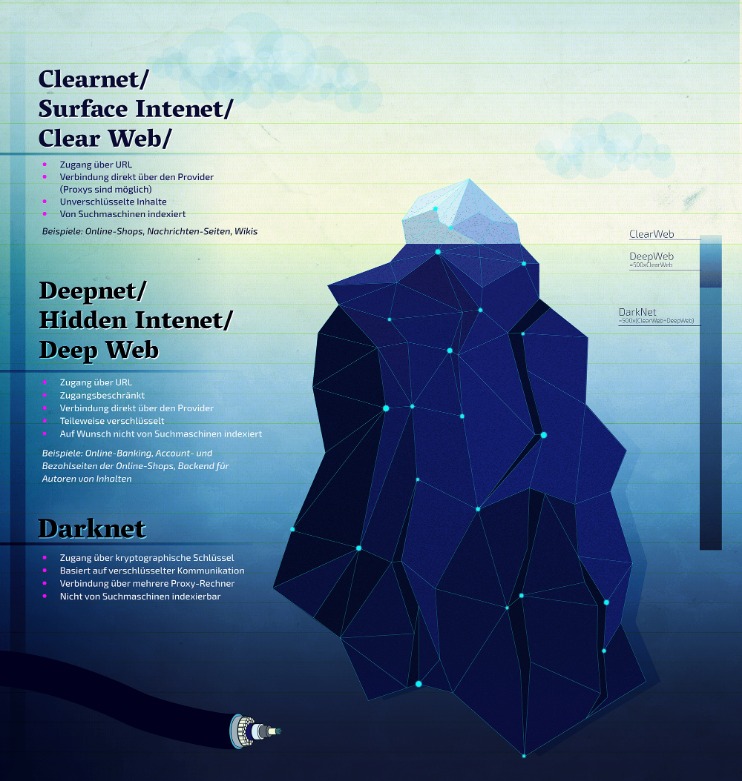
It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Business operational data, such as operational data, financial data, intellectual property, and trade secrets can be found on the dark web. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes. As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously.
The Escrow Process
For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection. However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities. Immediately close your entire Tor Browser window (not just that active tab).
Over time, ambitious individuals created infrastructure for these transactions, where for a fee, sellers have access to a digital ‘storefront’ to sell their products in a centralized marketplace. Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous. Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here. The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage.
Similar Sites
This marketplace accepts payments via Monero but also supports the Escrow system. Unlike traditional payment methods cryptocurrencies don’t require personal details like credit card numbers or bank accounts making the transactions more private. The darknet, also known as the dark web, is a concealed section of the internet that’s inaccessible via standard search engines. You can only access it using special software, settings, or authorization. This area comprises websites and content that are purposely kept hidden from public view. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
Simply download the file, install the software, and you’re ready to use its web-based interface. In opennet mode, the network will automatically assign you to other users on Freenet’s network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN.
Current Tor-Hoo Market List:
“A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers. Buy login credentials to a $50,000 Bank of America account, counterfeit $20 bills, prepaid debit cards, or a “lifetime” Netflix premium account.
Abacus alone represented nearly 5 per cent of total DNM revenue, underscoring the ongoing scale of underground commerce. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity.

There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. The dark web is a very popular platform for journalists, political bloggers and political news publishers, and in particular, those living in countries where censorship shields most of the internet. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project.

Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites. Unlike other search engines, it does not collect or share web activities and personal data of users. The generalizability is specific to Hydra and may not apply to other darknet markets or regions.
What Is The Dark Web? How To Access It And What You’ll Find
A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. The best way to protect yourself from the dangers of darknet markets is to simply avoid them altogether. Even browsing these sites can put you at risk of malware infections or attract unwanted attention from law enforcement. Some dark web listings claim to offer services like hacking-for-hire or even hitmen. Unlike surface web platforms, darknet markets have no reliable way to verify vendors.