This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacyRadar.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails.
Use Cryptocurrency For Transactions
These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack. I do not condone the use of DNMs to purchase or sell drugs and other illegal materials online. DNMs are inherently dangerous places and its users risk losing their money, their freedom, and their lives.Are you suffering from drug addiction?
Darknet Markets Explained: Navigating The Hidden Web
From there, these products are then passed on to distributors, which are the dark web marketplaces in this context. On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals.
Exodus Marketplace
It is similar to an online store, except it’s not the type you’ll find with a quick Google search. We will be exploring the top 10 Dark Web markets in this article. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. No matter where you browse the dark web from, you should exercise caution.
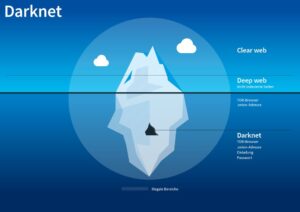
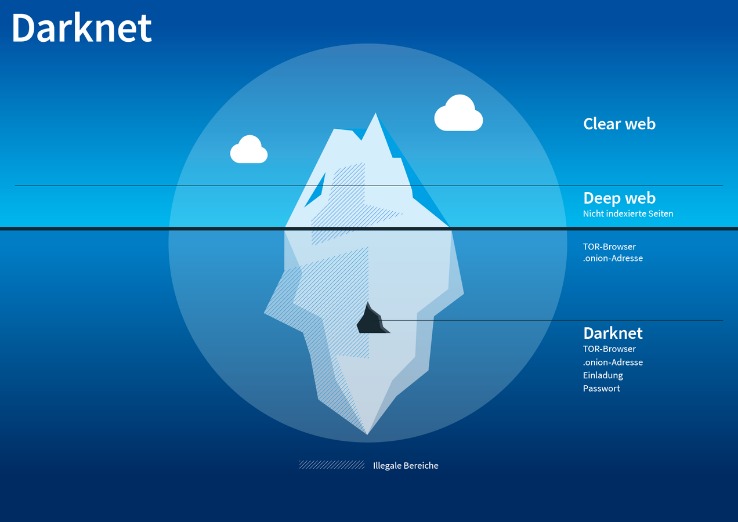
Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors. These hidden networks provide a platform for illegal activities that include the sale of stolen data, hacking tools, weapons, counterfeit currency, and narcotics. The dark web is a part of the internet that isn’t indexed by traditional search engines like Google—you can’t find it through standard browsing. It’s accessed using specialized software called Tor (The Onion Router), which anonymizes users and hides their locations.

Onion Links: How To Access Them
The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. A VPN protects your connection against everyone, not just your ISP and the authorities.
- They really don’t care about the loss and dilemma of the victims whose data has been stolen.
- People mostly use it for covert communication, anonymous tips submission, and stuff like that.
- You can also take a look at the blogs & essays section if you want to find some nifty coding resources.
- For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime.
- The Ahmia search engine also has a strict policy against “abuse material,” focusing on users’ protection from potentially dangerous content and malicious attacks.
The Rise Of 2024 Darknet Markets
There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together. Once you have those, there are several ways to tunnel through the dark web. Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny.
How To Gain Safe Access To The Dark Web Marketplaces
These hackers don’t hide in the shadows as much as you might think. Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles. Exodus Marketplace started to become popular after the shutdown of Genesis Market, and it replaced it successfully.

The lack of filtering increases the likelihood of encountering dangerous or illegal content, phishing attempts, and other security threats that can compromise your personal information and safety. Kilos offers multiple forums and dark web marketplaces for specified products. This search engine also offers advanced filtering, ensures fast search, and is known for illegal activities, so it is not recommended for general usage. Its extensive and unfiltered search results also attract cybercriminals, so it’s important to be extremely careful when using the Kilos dark web search engine. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information.

Tips To Stay Safe When Using The Dark Web
- Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser.
- Onion URLs generally contain a string of seemingly random letters and numbers.
- Its extensive and unfiltered search results also attract cybercriminals, so it’s important to be extremely careful when using the Kilos dark web search engine.
- Ahmia can also be used to view insights, news, and statistics about the Tor network.
- In fact, WeTheNorth is more of a private club than an open market – something its operators want.
It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. Although dark-web marketplaces utilize technologies like Tor and I2P to enhance anonymity, these methods are not foolproof. Law enforcement agencies continuously improve their ability to trace transactions and monitor marketplace activity.
Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
As a user or cybersecurity professional, approaching these marketplaces demands utmost caution, thorough knowledge of operational security, and constant awareness of legal boundaries. Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Understanding both the lawful and unlawful scenarios helps provide a balanced view of their practical applications in 2025. Finally, product variety significantly influences marketplace choice.
Even when using security measures and your common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed. Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used.