The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity.
How Do Scammers Get Digital Identity Information?
Our team understands the ins and outs of ID design, including state-specific details, holograms, UV ink, and scannable barcodes. We don’t just create IDs; we replicate them down to the smallest nuances that even professionals can’t detect. Our customization process ensures your ID doesn’t just look real—it fits your story. With us, you get an ID that’s tailored to you, down to the smallest detail. No fading, no peeling, no shortcuts—just IDs that withstand the test of time.
Is It Illegal To Enter The Dark Web?
Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment. In summary, beyond 2025, dark-web marketplaces will increasingly blend cutting-edge technologies with adaptive strategies to survive in an environment marked by heightened regulatory oversight and shifting user priorities. Users and cybersecurity professionals alike must stay informed and prepared to navigate this rapidly changing digital frontier. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats.

Advice For Consumers Thinking About Selling Their Face And Documents, On The Dark Web Or Not—Don’t
And if you want to start a Tony Montana-style drug empire, methamphetamine can be bought in bulk for $34,000 per kilo, and rocket launchers and explosives can be obtained for between $500 and $35,000. If you want to boost your social media presence, you can buy followers and likes. For between $4 and $400, you can buy guaranteed “ghost” followers and suddenly look like an internet sensation. Counterfeit cash can be purchased with an exchange rate as low as 10 per cent – just $95 can get you €1,000 in fake bills. Let’s get this straight — not everything on the dark web is illegal or harmful. In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored.
- Total no. of posts are 246,949 in 53, 901 threads and total registered members are 31,465.
- ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users.
- Taking these steps cannot eliminate all risks (exit scams and law enforcement still happen), but they significantly improve privacy and security when researching dark web markets.
- For sellers, it’s often about making money while staying off the radar.
- Deep learning tools can generate high-resolution facial composites and falsified document templates, complete with authentic-looking fonts, holograms, barcodes, and microtext.
- The cycle that initiates the black market for identity data begins through a ransomware attack, data breach or successful phishing attempt.
Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. From there, these products are then passed on to distributors, which are the dark web marketplaces in this context. On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site.
The site allows users to find and buy a vast variety of products and services. It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites.
Darknet Marketplace Alternatives
By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers. This marketplace specializes in a variety of illegal products, including drugs, counterfeit documents, and hacking tools. Our team searched the dark web and put together a list of the most active dark web marketplaces in order to assist you in monitoring illegal trade of products, cybercrime activity, and dark web trends in the dark web space.
Security Blogs

Want to strengthen your identity checks and cut fraud risks? Book A Demo with AiPrise to see how the platform fits into your workflow and helps you stay secure and compliant. A woman in New Brunswick had her account hijacked; what started as a simple Facebook login ended with her friends being scammed out of thousands.
Border Control And Airport Security
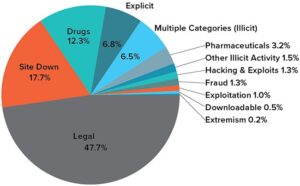
The below snap shot was taken from a credit card sales ad at a darknet market where a seller also provides advice on making less amount transactions per card to avoid getting detected. This blog focuses on explaining what darknet markets are, common payment model used, the type of digital data being bought and sold in the darknet markets and their typical costs. The objective of this blog is not to provide an exhaustive list of all the products and services being sold in the darknet markets but to shed light on how cybercriminals are utilizing the darknet markets to trade with impunity.
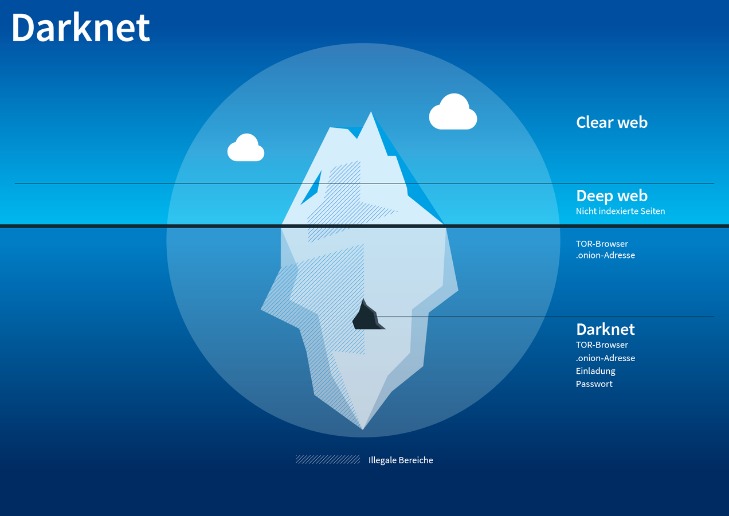
Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. Ideal marketplaces support anonymous browsing through networks like Tor and I2P, utilize privacy-focused cryptocurrencies such as Monero, and implement measures to prevent tracking and transaction tracing. Platforms that provide clear guidelines for maintaining operational security (OpSec) and offer built-in tools for data obfuscation are especially favored. Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers. The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud. Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project).

At its core, document fraud undermines trust, honesty, and transparency—essential components of a functional society. Individuals using fraudulent documents essentially bypass social and legal agreements that communities have established for collective well-being. Ethical concerns arise when one considers that fraudulent behaviors normalize deceit, creating an environment where dishonesty is increasingly accepted or justified, gradually eroding societal values. Ultimately, the severe legal and personal consequences far outweigh any perceived short-term advantages, underscoring the high-risk nature of using fraudulent identification documents. The Dutch National Police’s operation against Hansa Market in 2017 illustrates this approach.
Overall, Abacus Market distinguishes itself through rigorous security measures, effective moderation policies, and a strong emphasis on protecting user privacy. Despite minor accessibility inconveniences, these strengths have solidified its position among the top dark-web marketplaces in 2025. Overall, dark-web marketplaces in 2025 are more sophisticated, secure, and resilient than ever before, evolving rapidly in response to both technological advancements and intensified scrutiny from global law enforcement agencies. As the DNM builds a small pool of users and sellers, it will snowball into a lucrative operation IF the service remains reliable and secure. Besides ever increasing hosting costs, the site will have to contend with authorities, attacks from hackers, and the occasional disgruntled market administrator.
On the dark web, you don’t need to be a technical expert to design ransomware, and that’s dangerous. Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. They then use it to blackmail users until they pay a ransom. It’s also a marketplace for digital mercenaries; you’ll find everything from solo hackers offering their skills to well-organized groups that take on more complex or high-stakes projects. Some even have connections to criminal organizations and, in more serious cases, government-backed operations.