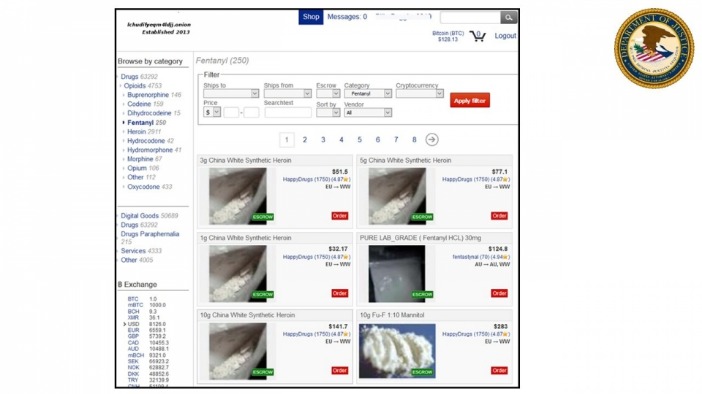
Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network.
In 2021, a small marketing firm experienced a devastating data breach after employee login credentials were compromised and sold on a dark web marketplace. The stolen credentials allowed attackers to infiltrate the company’s email system, impersonate senior staff, and send fraudulent invoices to clients. Within days, the attackers had exfiltrated sensitive client information, including proprietary marketing plans and billing data.

The Magical Comeback: Kaspersky And BIZONE Report New PipeMagic Activity In Saudi Arabia And Brazil
We also note that, interestingly, in certain markets, this security mechanism is missing if users access the market via the I2P network. The first screen users usually see after entering a market will be queuing, which is mainly used to protect the website from DDoS attacks. The market first puts the user into a queue and then automatically redirects to the next screen after waiting for a period of time. We also found that this mechanism should also include some sort of load balancing feature on the server side.
Far From Russia, A Pro-Moscow Sliver Of Land Tries To Cling To Its Identity — And Keep War At Bay
In fact, previous studies on DWM transaction networks have revealed crucial aspects of the ecosystem13,14,15. However, they have so far mainly focused on DWM users, without distinguishing between buyers and sellers, and neglecting the different weight that more active users may have in the system. The reason is that the operational structure of DWMs inherently hides the seller–buyer link, as all transactions are made through the marketplace. Buyers send money to the marketplace, which in turn sends the money to the seller.
Torch is one of the more established dark web search engines, designed to help users navigate the Tor network and discover onion sites. Unlike traditional search engines like Google or DuckDuckGo, Torch indexes hidden websites that operate beyond the reach of the surface web. But users should always be cautious and avoid clicking unfamiliar or untrusted links to steer clear of scams or malware. With law enforcement agencies improving their ability to track Bitcoin (BTC) transactions, darknet market operators and vendors are moving to Monero (XMR) as their cryptocurrency of choice. To analyse the connectivity of the whole ecosystem, i.e., how markets are connected with each other, we consider sellers and buyers that are simultaneously active on multiple platforms. In particular, multihomers that are sellers in multiple markets are multisellers, and similarly for buyers we have the multibuyers.
Cypher Marketplace
On the other hand, this increases the risk of fraud to buyers by vendors. Therefore, the market usually only allows vendors with a certain reputation (or that pay a certain deposit to the market in advance) to enable this function. This mechanism is, in general, more beneficial to vendors than to buyers, because it ensures a faster turnover of funds and mitigates the impact of market exit scams. It is not only used to display the identity in the market, but also is part of the account security mechanism. The minimum length of usernames is one character, but four characters is the most common minimum requirement.
How Is The Darknet Different From The Deep Web?
BriansClub remains a long-standing credit card data shop since at least 2014. Despite a 2019 breach that exposed over 26 million credit cards, it continues to operate, indicating sustained trust in its data pipelines. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using. This handy feature monitors the dark web for signs that your login details or other personal info have been leaked.
There’s no guarantee that placing an order with any DNM vendor will be safe or shipped. Functionally, accessing DNMs and using them requires quite a few extra steps to protect the anonymity of the buyers, sellers, and server admins. To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser. TOR Browser is a free, modified version of the Firefox web browser configured to connect to the TOR network.
Dark Web Markets: How They Work And Why They’re Dangerous
Server admins will have to either make special agreements to get initial sellers on board, or supply products themselves to get things started. Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures. This ongoing cat-and-mouse game poses a significant technical challenge in combating the activities within darknets. In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Once the buyer confirms satisfaction, the funds are released to the seller.
Darknet Communications In 2025 – From IRC Forums To Telegram Crime Networks
Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there. You can even find things such as BIN checkers and PayPal cookie converters. Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces. Now, that is not to say illegal behavior is completely beyond detection.
- These measures are essential for safeguarding sensitive data, maintaining regulatory compliance, and mitigating risks effectively.
- There is no need to visit darknet marketplaces yourself to know whether your data was leaked.
- The structural change seen in the multiseller network is not observed in the multibuyer network, as show in Fig.
- The website allows visitors to view all the goods and services on display before they buy something.
- Its founder, Ross Ulbricht, was arrested, and law enforcement took control of the site.
“But as scams on more blockchains including Ethereum, Tron, and Solana have grown, so too has the use of DeFi protocols,” the report noted. In 2024, DeFi played an increasing role in storing, transferring, and obfuscating illicit crypto proceeds. However, as one platform is taken down, another often rises in its place, adapting to the lessons learned from previous busts. The cycle is ongoing, with cybercriminals continually evolving their methods to avoid capture. Let’s keep sharing knowledge, staying safe, and working together to combat these underground threats.
These developments will likely enhance transaction security and reduce traceability, making darknet markets even more appealing to users worldwide. Moreover, a better and more detailed understanding of how rate limiting works may greatly improve the efficiency of crawlers and reduce manual labour. There are promising signs that we will soon be able to use a collection of scripts that can universally solve the kind of CAPTCHAs encountered in dark markets, which will be a very useful breakthrough. It is envisaged that machine learning techniques can be used to solve them quite easily in the near future. We are only able to cover the end-user side of security mechanisms, which may not be comprehensive.
Strengthen Authentication Systems
Stolen data can quickly transition from legitimate systems to underground forums, where it becomes a valuable commodity for cybercriminals. To counter these risks, organizations need robust, proactive solutions that go beyond traditional cybersecurity measures. This is where Brandefense’s Dark Web Monitoring Solution plays a critical role. People have been organizing illicit trades via the Internet since the 1970s. Those early examples, though, were through closed networks, and the actual exchanges of money and goods generally had to take place in person. With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy.
The dark web poses significant risks to small and medium-sized enterprises (SMEs), which are often ill-equipped to handle the sophisticated threats emerging from these hidden networks. Compromised credentials, stolen intellectual property, and leaked sensitive data regularly surface on dark web marketplaces, exposing SMEs to severe financial and operational consequences. Dark web marketplaces are structured platforms that mirror legitimate e-commerce websites but thrive on anonymity and untraceable transactions, often conducted through cryptocurrencies. According to a report by Kaspersky, a single stolen credit card can be purchased for as little as $15, while entire company databases are sold for significantly higher sums.
Some markets have services related to cybersecurity, while others might list more controversial items. The selection depends on the marketplace, and not everything found is legal. Alright, let’s get into the meat of it—the darknet markets that are ruling 2025. I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City. This isn’t just a quick list; it’s the full scoop on what they offer, how they keep things tight, and why they’re worth your time—or not. Whether you’re new to the dark web or a vet who’s seen it all, you’ll find something here to chew on.