All web pages not indexed by web crawlers are considered to be a part of the deep web. The content is generally more secure and clean than that of the surface web. However, cybersecurity organizations could benefit from indirect participation in discussions regarding hacking and exploit trading that regularly takes place on the dark web. This would give them insights into yet-unknown vulnerabilities and allow them to gain knowledge of exploits before they can turn into widespread cyber threats. While the deep web is chiefly used for legitimate day-to-day online activities, the dark web is mainly anonymous and known as a haven for conducting illegal transactions. The deep web is a section of the internet that cannot be indexed by web crawlers.
How To Safely Access The Dark Web?
Deep web, a part of the Internet that extends beyond the reach of search engines such as Google, Yahoo! The term “deep web” was coined in 2001 by computer scientist Michael K. Bergman, who differentiated it from the “surface web,” where openly viewable and retrievable content resides. The deep web is also known as the “invisible web” or “hidden web,” but it should not be confused with the “dark web,” where encrypted content with hidden IP addresses resides.
Doing so will protect you from accidentally accessing illicit content or becoming a victim of malware. Additionally, much of the materials on the dark web are illegal, and unknowingly downloading such content can implicate you in criminal activities punishable by laws. If your device is infected with malware, read our guide to remove malware from your computer. Visiting the dark web, if you don’t exercise caution and have enough security, poses many security and legal risks that can lead to data theft, identity fraud, and legal consequences.
What Is The Dark Web? How To Access It Safely?
It comprises many legitimate resources including academic databases, medical records, and private corporate networks. However, it is reasonable to know your content and ensure proper authorization. One should not undertake illegal activities such as accessing private data without consent, thereby risking further legal consequences. One must always respect the laws and regulations regarding privacy. The privacy offered by the Tor browser is important in the current digital age.
Safely Accessing The Deep Web And Dark Web
- Whited’s rule of thumb is to use the Tor Browser instead of Private Browsing Mode or Incognito Mode.
- Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs.
- So, that means that the number of pages increased by over 100 trillion in just over three years.
- Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators.
- While the deep web usually requires just a username and password to be accessed (think of your email inbox), the dark web cannot be reached without the right software or hardware.
- The answer, of course, is by using dark web browsers like the open-source platform Tor.
Simply download the file, install the software, and you’re ready to use its web-based interface. That alone might already raise suspicion and place you under special surveillance. Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. Next, disable Javascript in your Tor browser to prevent malicious scripts from attacking your browser sessions. You can disable Javascript by clicking on “Preferences” in the macOS app or “Settings” in the Windows app.
MULTI-LAYERED ENCRYPTION
Users need this browser to access this special category of websites. While the content on the dark web has the potential to be more dangerous, this content is usually walled off from regular users. However, it is entirely possible for regular users to accidentally come across harmful content while browsing the deep web, which is much more easily accessible. This makes deep web security important for individuals and enterprises alike. NordVPN allows you to create your private encrypted network for safe file sharing and work using its Meshnet feature.
The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks. Most likely, the native account on your device has full admin permissions by default. Many malware take advantage of this vulnerability to launch an attack. Therefore, you can prevent this exploitation by setting up a non-admin account. If you are in a position to report the incident safely, you should report it to the authorities immediately.
Method II – VPN Over Tor

We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. Additionally, check the Block pop-up windows and Warn when websites try to install add-ons settings. You should review access to your camera, location, and microphone regularly to ensure no website has unnecessary permissions. Additionally, many Internet Service Providers (ISPs) flag Tor usage as suspicious and may block access to the network altogether. The dark web is a playground for hackers, cybercriminals, and people with nefarious objectives.
Using the Tor Browser with a VPN is a safer and more secure option, as it provides end-to-end encryption and better privacy protection. A small, hidden part of the internet accessed via special tools like Tor, often linked to anonymity and sometimes illegal activities, but also used for legitimate purposes like secure communication. The deep web is largely used to protect personal information, safeguard databases and access certain services, whereas the dark web is often used to engage in illegal activities. It is also used for military/police investigations, political protests and anonymous internet browsing.
Avoid Dropping Personal Information On The Dark Web
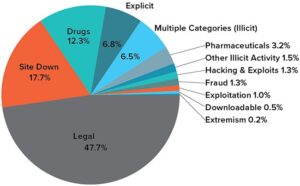
You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. Identity theft monitoring is critical if you want to keep your private information from being misused.
It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing.
How To Turn Off SafeSearch On Google, Bing, DuckDuckGo, Yahoo
Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search.

However, there’s no guarantee that all the links on this site are working. Some may lead to malicious sites, downloading malware on your device. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. However, please note this article is for research and educational purposes only. The dark net is full of notorious hackers, scammers, malware, and other viruses. We recommend using NordVPN and a robust antivirus like TotalAV to keep you safe while browsing the dark web.
It consists of private, secure, often password-protected, content requiring credentials or special access. Most activities on the deep web are legal and intended to protect user privacy. Tor (“The Onion Routing” project) network browser provides users access to visit websites with the “. This browser is a service originally developed in the latter part of the 1990s by the United States Naval Research Laboratory. All commonly public-facing websites accessed via traditional browsers like Google Chrome, Internet Explorer, and Firefox are contained here.
The internet’s deeper layers—namely, the deep web and dark web—represent distinctly different realms of online interaction. Understanding the fundamental differences between the two is crucial for safe navigation in today’s digital world. The dark web is the smallest part of the internet ecosystem—even smaller than the surface web.