Once the download is complete, the user needs to locate the file and double-click it to initiate the installation wizard. The wizard will guide the user through a series of steps, including selecting the preferred language and choosing an installation location on their computer. Following the prompts and clicking “Install” will complete the installation process. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet.
Https://g7ejphhubv5idbbu3hb3wawrs5adw7tkx7yjabnf65xtzztgg4hcsqqdonion/
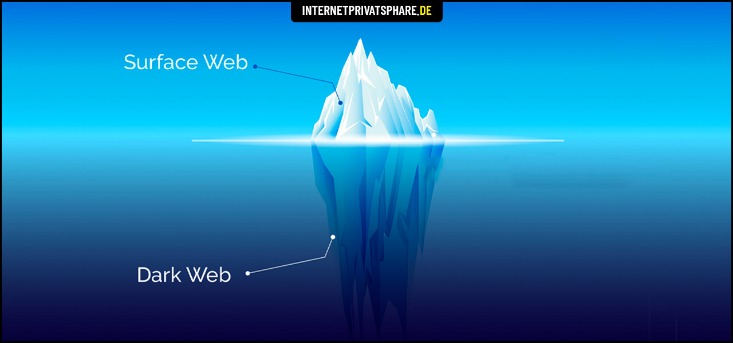
- So, what even is this dark web, and why are these marketplaces present there?
- Understandably, as in the case with most illicit trade markets, you don’t even need to verify your email Awazon.
- Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge.
- We must explain that Tor is safe on paper but practice has shown that this browser can fail you.
- (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top.
- On the regular web, domains such as are translated into their actual IP addresses via the domain name system (DNS).
This is partly due to their ephemeral nature and the privacy-centric design of the Tor network. As a result, users often rely on specialized search engines specifically designed to discover onion services. Examples of such search engines include DuckDuckGo (which also offers an onion service for privacy-enhanced searching), Ahmia, Torch, and DarkSearch.
Top VPN Deals
A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate. The extra connection layers can act as a significant burden to your browsing experience if you’re doing something that is bandwidth intensive. As we mentioned above, when you connect to Tor your data first goes through an entry node, which can see your IP address. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity. Most internet users love a question and answer forum like Reddit or Quora, on the surface web. The dark web version is Hidden Answers, where users can discuss a wide range of topics anonymously.
After the download, the user needs to open the .dmg file, which will mount a virtual drive containing the Tor Browser application. The standard procedure on macOS is then to drag and drop the Tor Browser application icon into the Applications folder to complete the installation. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges.
Download Tor Browser
ZeroBin encrypts and decrypts text in the browser, so their servers have no way of knowing what’s happening on the browser side. Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password. If you ever have to connect to public Wi-Fi, make sure to use a VPN to keep your browsing safe and private.
- Unlike conventional web addresses that rely on the Domain Name System (DNS) to translate human-readable names into numerical IP addresses, .onion addresses have a distinct structure and function.
- Once the download is complete, the user needs to locate the file and double-click it to initiate the installation wizard.
- According to Tor, on average about 2.6 million “clients” (users) directly connect to its network each day.
- If you need to protect or enhance your streaming, gaming, or torrenting activities, a Virtual Private Network (VPN) is a much better option as a secure connection to the net.
- If you’re new to Tor, setting up the browser software and connecting to the network might seem intimidating, but it’s actually straightforward.
Social Media
Using the Tor browser is simple, but knowing when to fire it up is more complicated. You could do all your browsing with Tor, though it’s slower than a standard browser, something the Tor Project is working hard at to improve, says Stephanie Whited, communications director for the Tor Project. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual. Enable MFA wherever possible to protect your accounts from unauthorized access. Hidden Answers is one of the biggest question-and-answer dark web sites. This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy.
Understanding The Risks: Potential Dangers Of The Dark Web
Using Tor is especially helpful in countries where authoritarian governments censor the internet, preventing citizens from accessing news outside their country. These URLs are usually very long, consisting of a random jumble of letters and numbers. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet.
Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors. By following these straightforward steps, you significantly reduce the risk of exposure, protect your digital identity, and ensure a secure and anonymous browsing experience on the Dark Web. The term “onion routing” reflects how layers of encryption are applied—similar to peeling layers from an onion. With each hop through the network, a layer of encryption is removed, concealing the user’s original location and identity. This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor.
onion URL Structure

Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing.

Words Of Caution When Using Dark Web Sites
Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search. We will be exploring the top 10 Dark Web markets in this article. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites.
In short, red rooms appear to be more of a modern-day urban legend than a verified reality, blending horror fiction with the fears of the digital age. Whistleblowing refers to the act of exposing unethical, illegal, or harmful practices within an organization. Individuals who blow the whistle, known as whistleblowers, play a crucial role in promoting transparency and accountability, often at significant personal risk. They may expose various issues, ranging from corporate fraud to governmental misconduct, in hopes of fostering change and ensuring the public’s right to know.
How To Safely Access The Dark Web With Tor — Step-by-Step Guide (
As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.

The oldest .onion links directory which is actively maintained up to date. This website is made public with the intention to aid the Internet users with navigation of the so called dark web. We have never received a compensation in any form for operating this website. We are not responsible for any harm or loss you may receive by following links listed on this site. Whether you are doing research, applying OSINT (Open Source Intelligence), or trying to get your head around what Dark Net really is. The question of how to look for information in the scary and super dupper dark corner of the Internet.
The key is to encrypt your traffic BEFORE you use Tor so that your ISP (Internet Service Provider) doesn’t see you’re in the Tor network. Hacked PayPal accounts, counterfeit money, drugs, weapons, and much more — the darknet is teeming with illegal offers. Another open-source project that requires attention is Mozilla Firefox. While it’s a major and very popular browser, it has privacy and security-oriented features that, for example, block tracking or ads, alert you of data leaks, or check the security of your passwords. With Mozilla Firefox, you also get access to a huge library of extensions to customize the browser. On top of that, you can count on frequent updates and security patches from the community of developers working on it.



